grub-live - boot an existing Host OS or VM into Live Mode

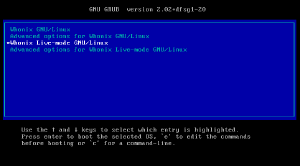
The grub-live package offers an additional "LIVE mode" boot menu entry for the GNU GRUB boot loader![]() .
.
This package is compatible with many Linux distributions, including Debian and Ubuntu. In Kicksecure and Whonix™ it is installed by default. Grub-live can be applied for a host operating system (OS) as well as for a guest OS on a virtual machine.
Compatibility[edit]
grub-live is compatible and tested with Debian, Kicksecure and Whonix. In Kicksecure and Whonix it is installed by default. It should also without any problems run on Ubuntu and other Linux distributions which implement Debian live boot. But due to little user adoption and testing at this point in time grub-live for those distributions is still labelled untested.
Installation / Getting started[edit]
The grub-live package is hosted under the grub-live GitHub repository![]() . There you will also find the installation guide.
. There you will also find the installation guide.
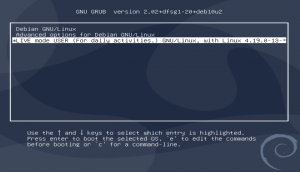
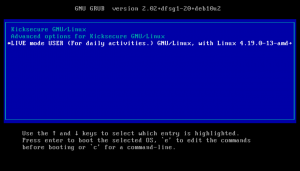
After the installation you can instantly use the Live Mode in your operating system. Simply boot/reboot your system and choose the new "LIVE mode" option in the boot menu. For Kicksecure specifically read: Detaillled documentation for using the live mode for Kicksecure.
[edit]
Optional.
If you have installed grub-live and you want the "LIVE mode" option to be the default selected option in your grub menu please follow the instructions below. Be aware however that due to little user adoption and testing yet this options is still labelled untested.
1. Do a grub-live package installation check
By default the grub-live package is installed in Kicksecure. If you boot your system and a boot menu entry "LIVE mode" is already avaialble, then grub-live is already installed.
Alternatively you can make sure the package grub-live package![]() is installed. The following command can be used to check on the command line if the package is already installed by default.
is installed. The following command can be used to check on the command line if the package is already installed by default.
dpkg -l | grep grub-live
2. Set LIVE mode as default boot menu entry
There are 2 ways to accomplish this. Choose one ot these options
Option (A) - symlink method
- Advantage: This is easier because updates to grub-live will be automatically applied.
- Disadvantage: There will be a duplicate live boot menu entry.
- Copy and execute the following command
sudo ln -s /etc/grub.d/11_linux_live /etc/grub.d/09_linux_live
Option (B) - moving method
- Advantage: No duplicate live boot menu entry.
- Disadvantage: Updates to grub-live will NOT be automatically applied.
- Copy and execute the following command
sudo mv /etc/grub.d/11_linux_live /etc/grub.d/09_linux_live
3. Re-generate grub boot menu
The grub boot menu needs to be regenerated for the changes to be applied. Copy and execute the following command
sudo update-grub
4. DONE
The process of changing from "live mode opt-in through boot grub menu" to "live boot by default" has been completed.
5. Updates
If in step 2 "option (B)" was chosen then this process might need to be repeated from time to time if there have been updates to GRUB or to your system. The need to repeat this process from step 1 to step 4 will be indicated as soon as the "LIVE mode" entry will not be the default entry in the GRUB boot menu anymore.
If in step 3 "option (A)" was chosen then this step is not needed. Updates will be applied automatically.
Get GRUB to remember your last choice (e. g. Live mode)[edit]
Optional.
If you don't want to set Live Mode as your permanent default boot option but still want the comfort of having GRUB remember your last choice, e. g. "Live mode", then follow these instructions. [1]
1. Open file /etc/default/grub.d/50_user.conf in an editor with root rights.
Others and Alternatives
- This is just an example. Other tools could achieve the same goal.
- If this example does not work for you or if you are not using Kicksecure, please refer to this link.
sudoedit /etc/default/grub.d/50_user.conf
2. Now add those two lines to this file: GRUB_DEFAULT=saved GRUB_SAVEDEFAULT=true
3. Finally execute this command: sudo update-grub
4. Done.
Your boot menu now remembers your last choice.
Alternative to grub-live[edit]
As an alternative to grub-live it is also possible to automatically detect
if the disk is set to read-only and enable live mode automatically using the
ro-mode-init package. Read
VM Live Mode - Alternative ro-mode-init Configuration
for further instructions.
ro-mode-init is currently less tested than grub-live.
Comparison between grub-live and Tails[edit]
Tails is its own operating system whereas grub-live is a package enabling Live Mode on different Linux distributions. The following table will show advantages and disadvantages of grub-live in regard to Tails. It shall be noted however that whereas Tails is optimized in regard to Live mode grub-live is vastly more compatible with other systems.
Table: Comparison of grub-live and Tails
| Aspect | grub-live on the host [2] / grub-default-live on the host |
Tails DVD only | Tails USB / DVD, with persistent USB | Tails read-only medium and other devices with write capability unplugged [3] [4] |
|---|---|---|---|---|
| Common [5] mode of operation | Yes | Yes | Yes | No [6] |
| Amnesic / protects against disk modifications [7] | Yes | Yes | Yes | Yes |
| Protects against malware persistence on hard drive after malware compromise | No [8] | No [8] | No [8] | Yes [8] |
| Protects against firmware trojans after malware compromise | No [8] | No [8] | No [8] | No [8] |
| Avoid writing to arbitrary (non-boot) host disks | ? | Yes [9] | Yes [9] | Yes [9] |
| Disables removable drives auto-mounting | No | Yes [10] [11] | Yes [10] | Yes [10] |
| Disables swap | ? | Yes | Yes | Yes |
| Disabled virtual machine shared folders | No [12] | ? | ? | ? |
| Wipe RAM on shutdown | No, but see ram-wipe. [13] | Yes, but with limitations. [14] | Yes, but with limitations. [14] | Yes, but with limitations. [14] |
| Wipe video RAM on shutdown | No [15] | No [16] | No [16] | No [16] |
| Emergency shutdown on USB removal | No | Yes | Yes | Yes |
| Live Mode Usability [17] | Average [18] | Good [19] | Good [19] | Good [19] |
| Live Mode Indicator | For Xfce only. [20] | Unneeded | Unneeded | Unneeded |
| Unified Amnesic + Anonymous User Experience | No [21] | Yes | Yes | Yes |
| Easy standard ("everyday") upgrades [22] | Yes | ? | ? | ? |
| Release upgrades [23] possible anytime [22] | Yes | No [24] | No [24] | No [24] |
| Live boot by default |
|
Yes | Yes | Yes |
| Persistent boot by default |
|
No | No | No |
| Full disk encryption compatibility | Yes | No | No | No |
| Encrypted persistence supported | Yes | Yes [26] | Yes [26] | Yes [26] |
Security Considerations[edit]
How secure and reliable is any live mode?
Computers typically default to data persistence rather than amnesia. Coupled with widespread computer security vulnerabilities (see About Computer (In)Security), implementing a secure system is challenging.
grub-live is relatively straightforward. It primarily involves installing necessary dependencies and setting kernel parameters (details in Implementation). However, the software it is based on, such as dracut (or initramfs-tools/Debian's live-tools), mount, overlayfs are complex. Sparse developer documentation in this area makes this difficult. There is also an increased risk of failures post Release Upgrade or after installing new major versions of Kicksecure or Debian, due to the generic nature of the solution.
There is a potential risk that malware could remount a read-only disk as read-write. While no confirmed cases exist, theoretically, even legitimate software could inadvertently perform such actions. To mitigate this risk, it's advisable to use grub-live in conjunction with a physical read-only mode for hard drives, where feasible. See read-only.
Using grub-live on the host operating system, combined with virtual machines (VMs), is a safer configuration. In this setup, any disk remounting as read-write within a VM would be negated upon rebooting the host. VMs, in this context, are unaware of the host's live mode status and cannot directly alter it.
Would using an ISO image be safer? Generally, yes. Because ISOs commonly aren't modified. It seems unlikely that an ISO would be inadvertently remounted as read-write, unless targeted specifically by malware.
Tools like growisofs can append data to an ISO, it's more complex than a simple remount command. Even without growisofs, Malware could potentially repack![]() and rewrite an ISO, but it is an even more complicated process. Not something that can happen by accident.
and rewrite an ISO, but it is an even more complicated process. Not something that can happen by accident.
What about read-only media, like a DVD-R (not DVD-RW)? This is indeed a safer option, but less practical. It requires burning the DVD, then using it in a read-only DVD reader, which is not a common practice. Such devices are not popular anymore nowadays.
Combining physical write protection switches with grub-live would further enhance security. However, even this is not foolproof due to potential hardware vulnerabilities or defects. Thus, it should be considered an additional layer of defense rather than a complete solution.
Reflecting on these aspects, we can categorize security configurations from least to most secure, as follows:
Notes:
- This list, created in December 2023, might have minor inaccuracies but generally represents the correct security hierarchy.
- ISO HDD: It is possible to boot an ISO located on the hard drive. This is unspecific to Kicksecure and out of scope for this documentation.
- VM live mode HDD boot without read-only VM HDD ("least secure")
- VM live mode HDD boot with read-only VM hard drive
- VM live mode ISO boot without VM HDDs connected
- host live mode HDD without read-only HDD
- host live mode HDD without read-only HDD + using VMs
- host live mode HDD with read-only HDD
- host live mode HDD with read-only HDD + using VMs
- host live mode ISO HDD with read-only HDD
- host live mode ISO HDD with read-only HDD + using VMs
- same as above but with Full Disk Encryption as an additional safety layer
- same as above but hardware write protection switches enabled
- host live mode ISO DVD-RW with
- host live mode ISO DVD-RW with + using VMs
- host live mode ISO DVD-R with
- host live mode ISO DVD-R with + using VMs
- same as above but with all other storage devices disconnected ("most secure")
Additional steps users can take to improve the security of live mode:
- Avoiding installation of additional software, especially more complex software that uses mount / loop devices or breaks the live indicator such as for example
snapd. - Prevention of Malware Sniffing the Root Password, because remount read-write requires root.
See also
Whonix technical design documentation on forensics
![]()
![]() .
.
In summary, while striving for maximum security, absolute guarantees are unattainable. Users seeking higher data amnesia assurances should consider becoming developers or auditors, or sponsoring focused development and review in the realm of anti-forensics, including the development of comprehensive automated testing frameworks.
Remount Disk as Read-Write after booting into Live Mode[edit]
This is chapter is more of developer documentation, proof of concept, for curiosity than something that users should do.
1. Create a mount folder /mnt/disk.
sudo mkdir /mnt/disk
2. Mount.
Note: /dev/sda3 applies to VirtualBox VMs. It needs to be replaced with the actual hard drive device name.
sudo mount /dev/sda3 /mnt/disk
3. Remount a read-write.
sudo mount -o remount,rw /dev/sda3 /mnt/disk
4. Do persistent modifications.
For example, create a file /home/test-file.
touch /mnt/disk/home/test-file
It is unclear if the disk could even be remounted to / but that is left as an sysadmin exercise to the reader.
5. When done, unmount.
sudo umount /mnt/disk
6. Remove the mount point.
Optional.
sudo rmdir /mnt/disk
7. Done.
The process has been completed.
Questions and answers:
- Is this a security issue? Yes.
- Is this issue specific to, caused by grub-live or Kicksecure? No, unspecific to Kicksecure.
- Is this issue reproducible on other live systems, i.e. without grub-live, Kicksecure being involved? Yes.
- Are also similar live systems affected? Yes, see Security Considerations.
- What users can do to improve their security? See same link as above.
Troubleshooting[edit]
Here are some problems you might encounter and their possible solutions.
[edit]
Please check your local file /etc/grub.d/11_linux_live
looks exactly the same as /etc/grub.d/11_linux_live on GitHub![]() to verify you have the latest version of the grub-live package. Note, that the stable version might look slightly different than the developers or testers version on github.
to verify you have the latest version of the grub-live package. Note, that the stable version might look slightly different than the developers or testers version on github.
Please run the following commands for debugging / information gathering and post them when creating any support requests.
dpkg-query -W -f='${db:Status-Status}' initramfs-tools
dpkg-query -W -f='${db:Status-Status}' dracut
Live Check Systray Issues[edit]
The live mode is indicated by a Live Check Systray icon. I can happen that this icon has an issues. If so here's what you can do.
First of all this is NOT an indication of compromise by malware. The real issue is as simple as: The Live Check Systray is broken.
Known issues:
- 1) As mentioned in chapter Combine Kicksecure Live VMs with Read-only Mode for Virtual Hard Drives chapter VirtualBox.
If not an already known issue, please follow these steps:
1. Is livecheck.sh showing an error?
If livecheck![]() is showing an error it might be the following issue. Live check runs command
is showing an error it might be the following issue. Live check runs command sudo --non-interactive /bin/lsblk --noheadings --raw --output RO as the current unprivileged user. You can test this for yourself with the following command. If this is working then this is NOT the issue
sudo --non-interactive /bin/lsblk --noheadings --raw --output RO
If this is not working the problem might be that this will only work by default for the user user![]() , no other user. For example it will not work by default for the Linux user account
, no other user. For example it will not work by default for the Linux user account user2 or any other than user.
If the problem is that a user other than user is the logged in subject then
- option (A) the current user - for example
user2- needs an exception in/etc/sudoers.d. For comparison see file/etc/sudoers.d/desktop-config-dist .
. - option (B) the current user - for example
user2- needs to be or become a member of any of the following Linux user groups:
users
staff
adm
sudo
root
wheel
console
console-unrestricted
2. Try lsblk
If the above method does not work try also this:
sudo /bin/lsblk
3. If nothing works, report the bug
If you are still having issues you can report a bug with the output from above two lsblk commands included from above.
Technical Details of livecheck.sh[edit]
This chapter is for advanced users only.
Most users can skip this chapter. See livecheck.sh![]() for further script details.
for further script details.
- The meaning of
0inlsblkoutput isread-write. - The meaning of
1inlsblkoutput isread-only.
If anything in coloumn RO is set to 0, then it is not blessed read-only hard drive mode.
Example lsblk without any snapd installed, Kicksecure, live mode, and read-only hard drive mode enabled.
sudo lsblk
NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT sda 8:0 0 100G 1 disk └─sda1 8:1 0 100G 1 part /lib/live/mount/medium
Example lsblk without any snapd installed, Kicksecure, live mode, and read-only hard drive mode disabled.
sudo lsblk
NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT sda 8:0 0 100G 0 disk └─sda1 8:1 0 100G 0 part /lib/live/mount/medium
Example lsblk with snapd and WickrMe installed, Kicksecure, persistent mode, and read-only hard drive mode disabled.
sudo lsblk
NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT loop0 7:0 0 62.1M 1 loop /snap/gtk-common-themes/1506 loop1 7:1 0 446M 1 loop /snap/wickrme/352 loop2 7:2 0 55M 1 loop /snap/core18/1754 sda 8:0 0 100G 0 disk └─sda1 8:1 0 100G 0 part /lib/live/mount/medium sr0 11:0 1 1024M 0 rom
Developer Information[edit]
Users can skip this chapter and below.
Implementation[edit]
This is based on dracut module 90overlay-root which gets enabled when kernel parameter rootovl is set. 90overlay-root is only available in the Debian fork of dracut.
- dracut module source file: /usr/lib/dracut/modules.d/90overlay-root/overlay-mount.sh
grub-livesource code
- main file:
/etc/grub.d/11_linux_live
- https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1017039

- https://github.com/dracutdevs/dracut/issues/1565

Development[edit]
Should port to 90overlayfs![]()
rd.live.overlay.overlayfs=1 rd.live.overlay.readonly=1
While Debian did not https://salsa.debian.org/debian/dracut/-/merge_requests/20![]() the module will be updated in the next major version of Debian as per usual as Debian receives newer dracut versions from dracut upstream.
the module will be updated in the next major version of Debian as per usual as Debian receives newer dracut versions from dracut upstream.
Porting grub-live to other Linux Distributions[edit]
Might be rather simple in comparison to other packages.
grub-live should already be compatible with any Debian based distribution as mentioned on top of this wiki page. Testing is very limited.
Qubes support:
- That would require packaging grub-live for Fedora.
- Or as a first step copying over the config files.
What grub-live technically in essence does:
- 1) The grub-live is just shipping 1 grub config file
/etc/grub.d/11_linux_live .
. - 2) Pull required dependencies in
debian/control
- 3) Postinst runs: "
sudo update-grub"
Footnotes[edit]
- ↑
Based on this askubuntu answer
 .
.
- ↑ Meaning,
grub-liveoutside of a virtual machine. Forgrub-livein a VM, see Live Mode. - ↑ Assuming Tails on a DVD which can only be written to once, not DVD-RW.
- ↑ Or using Tails USB with a physical, active, and effective (non-circumventable by software) write protection switch enabled.
- ↑ As in a substantial user group willing and able to do this.
- ↑ This would be a prudent approach but search engines indicate that no or very few users run this configuration.
- ↑ Excluding malware compromise.
- ↑ 8.0 8.1 8.2 8.3 8.4 8.5 8.6 8.7 Once targeted malware is active it can circumvent read-only settings, mount the harddrive, and add malware which becomes active after next boot.
- ↑ 9.0 9.1 9.2
Quote https://tails.boum.org/contribute/design/

Tails takes care not to use any filesystem that might exist on the host machine hard drive, unless explicitly told to do so by the user. The Debian Live persistence feature is disabled by passing
nopersistenceover the kernel command line to live-boot. - ↑ 10.0 10.1 10.2
Quote https://tails.boum.org/contribute/design/#index39h3

Removable drives auto-mounting is disabled in Tails 0.7 and newer.
https://gitlab.tails.boum.org/tails/tails/-/blob/master/config/chroot_local-includes/etc/dconf/db/local.d/00_Tails_defaults

- ↑
https://gitlab.tails.boum.org/tails/tails/-/blob/master/config/chroot_local-includes/etc/dconf/db/local.d/00_Tails_defaults
 contains a configuration for GNOME only. This is reasonable in the Tails context since its default desktop is GNOME and others are unsupported.
contains a configuration for GNOME only. This is reasonable in the Tails context since its default desktop is GNOME and others are unsupported.
- ↑ Considered a feature or bug?
- ↑
- https://forums.whonix.org/t/is-ram-wipe-possible-inside-whonix/5596

- https://github.com/QubesOS/qubes-issues/issues/1562

amnesiacould depend on bothgrub-liveandwiperamto simplify live boot for users. - https://forums.whonix.org/t/is-ram-wipe-possible-inside-whonix/5596
- ↑ 14.0 14.1 14.2 https://tails.boum.org/contribute/design/memory_erasure/

- ↑
https://github.com/QubesOS/qubes-issues/issues/1563

- ↑ 16.0 16.1 16.2 https://gitlab.tails.boum.org/tails/tails/-/issues/5356

- ↑ The user being aware of currently running in live mode vs persistent mode.
- ↑ Without Live Mode Indicator (see below) it is not obvious to the user if they booted into persistent or live mode. This might lead to a mistake where live boot is not selected from the grub boot menu (persistent mode is instead set), but the user believes otherwise.
- ↑ 19.0 19.1 19.2 Consistently good because amnesia has always has been a core Tails feature. It is obvious to the user that nothing persists except folders that have selective persistence enabled.
- ↑
https://github.com/Kicksecure/desktop-config-dist

- ↑ Kicksecure is primarily run inside virtualizers.
grub-liveis an extra configuration step on the user's host. - ↑ 22.0 22.1 Using standard package managers such as
apt. - ↑ Such as from Debian
stretchto Debianbuster. - ↑ 24.0 24.1 24.2 Release upgrade of Tails from lets say Debian
stretchto Debianbusteris a non-trivial development effort. See also: https://tails.boum.org/doc/upgrade/
- ↑ 25.0 25.1 Persistent boot is the default option in grub boot menu.
- ↑ 26.0 26.1 26.2 https://tails.net/doc/persistent_storage/index.en.html

Unfinished: This wiki is a work in progress. Please do not report broken links until this notice is removed, use Search Engines First and contribute improving this wiki.

We believe security software like Kicksecure needs to remain Open Source and independent. Would you help sustain and grow the project? Learn more about our 12 year success story and maybe DONATE!