Anbox - Run Android Applications and Games
https://anbox.io/![]()
redirects to https://github.com/anbox
![]()
which says it is deprecated.
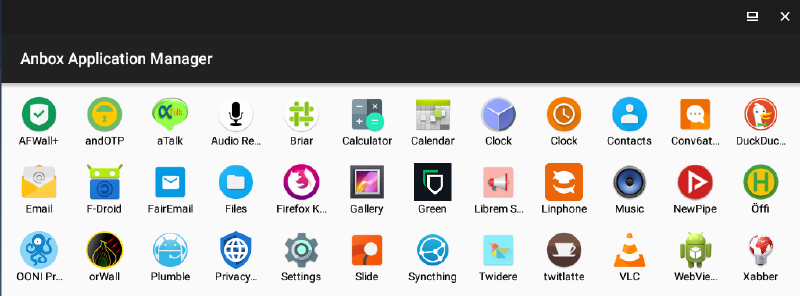

Anbox allows Android applications and mobile games to run inside Whonix.
Introduction
[edit]
Installation
[edit]To use Anbox with Whonix, apply the following steps.
1. Follow the general Kicksecure™ specific instructions.

2. Follow Whonix specific instructions.
3. Done.
Other Whonix specific notices can be found below.
Anbox Configuration
[edit]Derivative Specific
[edit]Disabling Whonix-Workstation™ Firewall is unfortunately required. Otherwise there would be no network access. [1]
1. Inside Whonix-Workstation.
(Qubes-Whonix™: inside StandaloneVM (better!) or Template).
sudo systemctl mask whonix-firewall
2. Disable systemcheck![]()
in Whonix-Workstation Firewall.
Open file /etc/systemcheck.d/50_user.conf in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/systemcheck.d/50_user.conf
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/systemcheck.d/50_user.conf
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/systemcheck.d/50_user.conf
Paste.
systemcheck_skip_functions+=" check_whonix_firewall_systemd_status "
Save.
3. Reboot.
This is required to unload Whonix-Workstation firewall rules and to have Anbox load its firewall rules.
sudo reboot
Android x86 as a Workstation
[edit]There are both distinct advantages and disadvantages of running Android applications in Android x86 Workstation. [3]
| Category | Notes |
|---|---|
| Bootloader / Ramdisk | It is possible to use Magisk to achieve root permissions and hide root from applications on Android x86. [4] |
| Flexibility |
|
| Networking | Android x86 provides a virtual Wi-Fi interface (wlan0) so applications think that a real Wi-Fi connection is established (Anbox uses a bridge network interface).
|
| Operating System | The full Android stack implemented as Android x86 is a full operating system which requires hardware virtualization. |
| Security | This configuration is less secure than utilizing a Whonix-Workstation. [6] |
| Software | Any version of Android from 4.x to 9.x can be installed. |
| Speed | This configuration is slower than anbox installation as Android x86 VM does not provide any type of Guest Additions meaning no graphic card drivers are supported. |
To check running anbox within kicksecure (same applied for Whonix-Workstation) check Anbox inside Kicksecure ™ Advantages and Disadvantages![]()
Forum Discussion
[edit]- Running Android Apps inside Whonix-Workstation - Anbox - Proof of concept

- Integrate Anbox into Whonix-Workstation

Footnotes
[edit]- ↑ This is because Anbox comes with its own bridged network. Whitelisting that interface in Whonix-Workstation firewall is undocumented and might require source code modifications. Patches are Welcome.
- ↑
- ↑ https://forums.whonix.org/t/integrate-anbox-into-whonix-workstation/9642

- ↑ Some individuals have already achieved this.
- ↑ Also, it may be possible to run ssh-server on Whonix-Workstation and connect the Android x86 through Termux or similar.
- ↑ Although it may have more flexibility, as static IP connections on the Android x86 Workstation have been accomplished.

We believe security software like Whonix needs to remain open source and independent. Would you help sustain and grow the project? Learn more about our 14 year success story and maybe DONATE!

















