Configure (Private) (Obfuscated) Tor Bridges
Censorship Circumvention. Get around network bans. Using Whonix with (private) (obfuscated) bridges. Useful in case your Internet Service Provider (ISP) bans or throttles connections to the Tor public network.
Bridges Description and User Groups
[edit]Introduction
[edit]When Tor is used with Whonix in the default configuration, anybody observing the properties of its application protocol can discover its presence. Potential observers include the Internet Service Provider (ISP), advanced adversaries, censorship enforcement bodies and other interested parties.
Tor bridges ("Tor bridge relays")![]()
are alternative entry points to the Tor network, acting as substitutes to regular Tor guards rather than an additional hop to the 3 hop journey. Not all bridges are obtainable publicly. Using a bridge makes it harder, but not impossible, for the ISP to determine if a user is connecting to Tor.
Intended User Groups
[edit]For the majority of Whonix users, connecting to Tor with the default configuration is appropriate and will work successfully. The minority of users requiring a bridge normally fall into three categories: [1]
- Tor is blocked, and some way - any way - to reach the network has to be found. The adversary is not very dangerous, but very annoying.
- Tor may or may not be blocked, but the users are trying to hide the fact they're using Tor. The adversary may be extremely dangerous.
- Other bridge users: Testing whether the bridge works (automated or manual), probing, people using bridges without their knowledge because they came pre-configured in their bundle.
The first group of users is only concerned with circumventing Tor censorship that is based on IP address or fingerprinting of protocols. Circumvention is necessary because Whonix would otherwise be rendered useless for most activities except working offline on documents and so on, since all Internet traffic is routed through Tor by default. This group is not worried about hiding the use of Tor and will need to use bridges or possibly other circumvention tools.
The second user group is unable to safely start Whonix in the default configuration due to Tor being considered dangerous or suspicious in their locality. In this case private bridges should be utilized instead of public obfuscated bridges, as this makes it harder (not impossible) to detect Tor. [2]
Note that the meek_azure pluggable transport may be necessary to deal with highly aggressive ISP censorship or national firewalls, like those found in China and the Middle East.
The third group is only concerned with testing bridge connections.
Before Configuring a Bridge
[edit]Users falling into one of the three groups described above should consider using Tor bridges. Before taking this step, please review The Tor Project's dedicated bridges page![]()
to better understand their design and operation. It is also recommended to review how Obfsproxy works
![]()
, since it is the most commonly used application for connecting bridges.
Always remember that bridges are not bullet-proof. The following is a reminder about bridge versus non-bridge anonymity:
Quote![]()
Roger Dingledine, cofounder
![]()
of Tor
![]()
:
[...] Bridges are less reliable and tend to have lower performance than other entry points. If you live in a uncensored area, they are not necessarily more secure than entry guards. [...]
Quote question:
If that is true, that also means, that bridge users are sufficiently more vulnerable to attacks, which are circumvented by entry guards?
Quote![]()
Roger Dingledine, cofounder of Tor:
[...] They're probably more vulnerable, but I don't know if I'd say "sufficiently". [...]
If a user is only concerned with connectivity (getting Whonix connected) and local ISPs do not usually hinder connections to the public Tor network, then something simpler than Bridges can be tried; see: Better Connectivity without Real Censorship Circumvention.
Additional Information and Recommendations
[edit]When deciding on the type of bridge to configure, it is recommended to:
- Prefer obfuscated bridges

, since they are harder to identify than other bridges.
- Use less well-known bridges, since it is safer. [3]
- Avoid using a meek provider that also runs DNS core servers, like Google's (now defunct) bridge. [4]
- Note that domain fronting has been pulled by Google and Amazon

, limiting the meek pluggable transport options to
meek_azureonly in Anon Connection Wizard. - For greater safety, use a private obfuscated bridge run by a trusted friend or organization in a different country. In this case "private" means that the bridge is configured with the option PublishServerDescriptor 0. [5]
Please note that it has been assessed as difficult beyond practicality to Hide Tor use from the Internet Service Provider with proxies, bridges, VPNs or SSH tunnels.
Finding a Bridge and Choosing the Right Protocol
[edit]In order to use bridges, the address of at least one bridge must be known in advance. It is preferable to have a private obfuscated bridge because the alternative -- public obfuscated bridges -- are more likely to be censored, since they are publicly listed. The Tor Project distributes public bridge addresses in several ways, including from their website![]()
and via email. The easiest way to find a list of public bridges is from The Tor Project Bridge Database
![]()
.
In early 2017, The Tor Project advice regarding recommended bridges changed: [6] [7]
... in Tor Browser to obfs4, given that we now have several high capacity obfs4 bridges and obfs4 is more likely to work in more regions than obfs3."
As time has gone on, more obfs4 bridge operators have come online, and obfs4 is now routinely recommended by Tor developers over obfs3, because the former: [8]
... should be able to defend more effectively against active probing.
As a consequence, obfs3 bridges have been deprecated as a configurable pluggable transport option in Tor Browser. [9] [10] Also see: obfs4 Transport Evaluation![]()
. [11]
The Tor Project provides a database of public obfs4 bridges![]()
. A more exhaustive list of public obfuscated bridges is available at The Tor Project Bridge Database
![]()
. obfs and obfs2 bridges are no longer available since they: [12]
... are now deprecated and were replaced by obfs3 . . . and obfs4.
Do not select the "IPv6 compatible" check box when sourcing bridges![]()
from the database, as they cannot be used in Whonix
![]()
yet.
How to Use Bridges in Whonix
[edit]It is possible to configure obfs4 and meek_azure (meek lite![]()
) bridges.
Two options. Choose either option A) or B).
- A) Anon Connection Wizard GUI application - recommended for most users. See instructions below. Or,
- B) Manual Bridge Configuration - advanced users.
1 Start Anon Connection Wizard.
If you are using Qubes-Whonix™, complete the following steps.
Qubes App Launcher (blue/grey "Q") → Whonix-Gateway™ ProxyVM (commonly named sys-whonix) → Anon Connection Wizard
If you are using a graphical Whonix-Gateway, complete the following steps.
Start Menu → Applications → System → Anon Connection Wizard
If you are using a terminal emulator (such as for example qterminal) on Whonix-Gateway, type.
anon-connection-wizard
If you are using a CLI Whonix-Gateway, see footnote. [13]
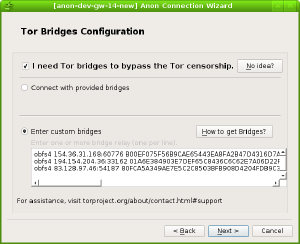
2 Use the Bridge Configuration Page
Choose option A or B.
A Anon Connection Wizard has some built-in bridges. To use them, complete the following steps.
Select "Configure" in the beginning page → Select "I need Tor bridges to bypass the Tor censorship" → Select "Connect with provided bridges" → Select a transport type that is suitable.
B If none of the default bridges work, the user can try to obtain a set of bridges manually. See Finding a Bridge and Choosing the Right Protocol. After obtaining a set of Tor bridges, complete the following step.
Select "Configure" in the beginning page → Select "I need Tor bridges to bypass the Tor censorship" → Select "Enter custom bridges" → Copy and paste the set of bridges to that input box(one bridge per line)
3 Done.
Bridge configuration in Anon Connection Wizard is complete.
Experimental Bridges
[edit]lyrebird
[edit]lyrebird![]()
is the successor to the obfs4proxy
![]()
package, which contained all stable pluggable transports
![]()
maintained by the Tor Project. It is also known as Tor's anti-censorship plugin.
It currently includes the obfs4, Snowflake, meek and WebTunnel pluggable transports.
It is currently not included in Whonix by default for several reasons.
But you can install and use it manually by following this guide:
1 Sysmaint Notice
2 Open the Tor AppArmor settings:
Open file /etc/apparmor.d/local/system_tor in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/apparmor.d/local/system_tor
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/apparmor.d/local/system_tor
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/apparmor.d/local/system_tor
3 Edit.
Scroll down near the end of the file and find the code containing ## obfsproxy.
Add an empty line above it, then add this:
## lyrebird /usr/bin/lyrebird rix,
4 Close and save the file.
5 If you want to use the latest version of Tor, see Newer Tor Versions![]() .
.
6 Clearnet Whonix-Gateway System DNS.
Whonix-Gateway System DNS is required when using DNS hostnames. [14]
1 Apply the following changes to Whonix-Gateway™.
Open file /etc/resolv.conf.whonix in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/resolv.conf.whonix
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/resolv.conf.whonix
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/resolv.conf.whonix
2 Uncomment the line #nameserver 10.0.2.3.
Remove the hash ("#") before nameserver. This means you should change #nameserver 10.0.2.3 to nameserver 10.0.2.3.
3 Follow platform-specific steps:
- Non-Qubes-Whonix: Done.
- Qubes-Whonix™: This should typically work. If not, refer to the footnote. [15]
4 Done.
The configuration for Whonix-Gateway System DNS is complete.
5 Note for wiki editors.
Once Whonix 17.2.2.6 (Non-Qubes-WHonix) / 18.1.5.9 (Qubes-Whonix) or above is released, anon-dns![]()
can be used and then the DNS enabling part can be simplified.
7 Download lyrebird.
You must download and install lyrebird manually because it is unavailable in the major package repositories.
The easiest way to install it is to use a precompiled version from the Tor Expert Bundle, which you can download here:
Tor Project download page![]()
You can also build the lyrebird executable yourself![]()
.
Copy the correct "Stable" link for your device type and architecture, then use this command to download it:
Note: Replace https://replace_with_download_url/file-name.tar.gz with the actual download link.
- Platform specific.
- Non-Qubes-Whonix:
- scurl https://replace_with_download_url/file-name.tar.gz -o tor-expert-bundle.tar.gz
- Qubes-Whonix:
- scurl --proxy http://127.0.0.1:8082 https://replace_with_download_url/file-name.tar.gz -o tor-expert-bundle.tar.gz
- Non-Qubes-Whonix:
8 Digital software signature verification.
Verifying Software Signatures![]() is recommended for Advanced Users.
is recommended for Advanced Users.
For that, you first have to download the .asc file, which is provided for the Tor Expert Bundle that you downloaded.
Return to your previous command by clicking the "up" arrow key on your keyboard.
Add .asc to both of your lines ending with .tar.gz:
https://replace_with_download_url/file-name.tar.gz.asc -o tor-expert-bundle.tar.gz.asc
Download the file and follow the instructions here![]()
to verify the signature.
The signature verification instructions in the link apply to both the Tor Browser and the Tor Expert Bundle, so ignore the text about verifying the Tor Browser and replace the filenames with yours. (tor-expert-bundle.tar.gz and tor-expert-bundle.tar.gz.asc)
Proceed with the next steps after successfully verifying the main file.
9 Extraction.
After verifying the signature, extract the bundle file:
tar -xvf tor-expert-bundle.tar.gz
Run the following commands from the directory in which you extracted the bundle:
10 Install lyrebird system-wide.
sudo cp tor/pluggable_transports/lyrebird /usr/bin/
11 Make lyrebird executable.
sudo chmod +x /usr/bin/lyrebird
12 Open the Tor configuration override file.
Tor configuration file.
Open the file /usr/local/etc/torrc.d/50_user.conf in a text editor![]() of your choice with administrative rights.
of your choice with administrative rights.
1 Sysmaint notice.
Ensure the VM has administrative (sudo / root) access first. See also sysmaint.
2 Platform specific. Select your platform.
Graphical Whonix-Gateway SYSMAINT Session
If you are using a graphical Whonix-Gateway booted into PERSISTENT Mode | SYSMAINT Session, take the following step.
System Maintenance Panel → Open Terminal → run /usr/libexec/gateway-shortcuts/torrc
Graphical Whonix-Gateway Unrestricted Admin Mode
If you are using a graphical Whonix-Gateway and enabled unrestricted admin mode![]() , take the following step.
, take the following step.
Start Menu → System Tools → Tor User Config
If you are using Qubes-Whonix™, take the following step.
Qubes App Launcher (blue/grey "Q") → Service → Whonix-Gateway™ ProxyVM (commonly named sys-whonix) → Tor User Config
13 Add the following.
Notes:
- Replace
Bridge webtunnel ...with actualBridgeconfiguration because...is only a placeholder. - Enter one or more bridges that you already have, or get bridges from the Tor Project using your preferred method: Tor Project instructions for obtaining bridges

ClientTransportPlugin webtunnel,snowflake,meek,obfs4 exec /usr/bin/lyrebird Bridge webtunnel ...
14 Save the changes.
15 Optional: Tor Configuration Check
16 Shut down.
Shut down the session.
17 Boot into user session.
Check whether your Tor connection works in the Tor Control Panel. Note: Unsuitable Connectivity Troubleshooting Tools
Select Bridges type: None as the connection method there. As a result, Whonix's default configuration file will be overwritten by your custom torrc (Tor configuration file).
18 Updates.
To update lyrebird, repeat the download steps above and replace the existing binary in Whonix-Gateway.
19 Done.
lyrebird has been installed and configured for manual use.
You can follow the Whonix forum thread related to this guide:
Adding WebTunnel bridges to Whonix forum thread![]()
Snowflake
[edit]Introduction of Snowflake
[edit]Snowflake is: [16]
...a pluggable transport
that proxies traffic through temporary proxies using WebRTC
, a peer-to-peer protocol with built-in NAT punching. It aims to work kind of like flash proxy, but without flash proxy's problems with NAT.
Setup Snowflake
[edit]On Whonix-Gateway.
1 Edit the Tor configuration file.
Tor configuration file.
Open the file /usr/local/etc/torrc.d/50_user.conf in a text editor![]() of your choice with administrative rights.
of your choice with administrative rights.
1 Sysmaint notice.
Ensure the VM has administrative (sudo / root) access first. See also sysmaint.
2 Platform specific. Select your platform.
Graphical Whonix-Gateway SYSMAINT Session
If you are using a graphical Whonix-Gateway booted into PERSISTENT Mode | SYSMAINT Session, take the following step.
System Maintenance Panel → Open Terminal → run /usr/libexec/gateway-shortcuts/torrc
Graphical Whonix-Gateway Unrestricted Admin Mode
If you are using a graphical Whonix-Gateway and enabled unrestricted admin mode![]() , take the following step.
, take the following step.
Start Menu → System Tools → Tor User Config
If you are using Qubes-Whonix™, take the following step.
Qubes App Launcher (blue/grey "Q") → Service → Whonix-Gateway™ ProxyVM (commonly named sys-whonix) → Tor User Config
2 Paste the following setting. [17]
UseBridges 1 ClientTransportPlugin snowflake exec /usr/bin/snowflake-client Bridge snowflake 192.0.2.3:80 2B280B23E1107BB62ABFC40DDCC8824814F80A72 fingerprint=2B280B23E1107BB62ABFC40DDCC8824814F80A72 url=https://1098762253.rsc.cdn77.org/ fronts=www.cdn77.com,www.phpmyadmin.net ice=stun:stun.l.google.com:19302,stun:stun.antisip.com:3478,stun:stun.bluesip.net:3478,stun:stun.dus.net:3478,stun:stun.epygi.com:3478,stun:stun.sonetel.com:3478,stun:stun.uls.co.za:3478,stun:stun.voipgate.com:3478,stun:stun.voys.nl:3478 utls-imitate=hellorandomizedalpn Bridge snowflake 192.0.2.4:80 8838024498816A039FCBBAB14E6F40A0843051FA fingerprint=8838024498816A039FCBBAB14E6F40A0843051FA url=https://1098762253.rsc.cdn77.org/ fronts=www.cdn77.com,www.phpmyadmin.net ice=stun:stun.l.google.com:19302,stun:stun.antisip.com:3478,stun:stun.bluesip.net:3478,stun:stun.dus.net:3478,stun:stun.epygi.com:3478,stun:stun.sonetel.net:3478,stun:stun.uls.co.za:3478,stun:stun.voipgate.com:3478,stun:stun.voys.nl:3478 utls-imitate=hellorandomizedalpn
3 DNS resolving in Whonix-Gateway.
Snowflake-client needs to resolve the -front domain to an IP address, in order to connect to the server; however, this DNS resolving will fail with the default Whonix gateway DNS configuration.
Clearnet Whonix-Gateway System DNS.
Whonix-Gateway System DNS is required when using DNS hostnames. [18]
1 Apply the following changes to Whonix-Gateway™.
Open file /etc/resolv.conf.whonix in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/resolv.conf.whonix
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/resolv.conf.whonix
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/resolv.conf.whonix
2 Uncomment the line #nameserver 10.0.2.3.
Remove the hash ("#") before nameserver. This means you should change #nameserver 10.0.2.3 to nameserver 10.0.2.3.
3 Follow platform-specific steps:
- Non-Qubes-Whonix: Done.
- Qubes-Whonix™: This should typically work. If not, refer to the footnote. [19]
4 Done.
The configuration for Whonix-Gateway System DNS is complete.
5 Note for wiki editors.
Once Whonix 17.2.2.6 (Non-Qubes-WHonix) / 18.1.5.9 (Qubes-Whonix) or above is released, anon-dns![]()
can be used and then the DNS enabling part can be simplified.
4 Restart Tor.
Platform specific. Select your platform.
Qubes App Launcher (blue/grey "Q") → Whonix-Gateway™ ProxyVM (commonly named 'sys-whonix') → Restart Tor
Terminal
Restart Tor.
sudo service tor@default restart
Check Tor's daemon status.
sudo service tor@default status
It should include a a message saying.
Active: active (running) since ...
In case of issues, try the following debugging steps.
Check Tor's config.
anon-verify
The output should be similar to the following.
/===================================================================\ | Report Summary | \===================================================================/ No error detected in your Tor configuration.
5 Done.
The procedure is complete.
Snowflake forum discussion:
- https://forums.whonix.org/t/replacing-meek-snowflake/5190

- https://forums.whonix.org/t/use-snowflake-in-whonix-to-bypass-tor-censorship/13441

Optional Snowflake Configuration
[edit]Use AMP cache rendezvous for Snowflake
[edit]Optional.
wkrp stated in a post![]()
:
by default in Tor Browser, Snowflake does rendezvous using a domain-fronted HTTPS request. Now there is an alternative (backup) to domain fronting rendezvous: AMP cache rendezvous. If one rendezvous method is blocked, there is a chance the other will work.
Replace the second line in /usr/local/etc/torrc.d/50_user.conf with:
Debugging Snowflake
[edit]Snowflake Usage Verification
[edit]Optional.
Make sure Tor is using snowflake.
To check if Tor is indeed using snowflake, we use nyx or onioncircuits. We are connecting to the Tor network through snowflake if:
- In
nyx, the guard node is a local address, like192.168.0.1; - or in
onioncircuits, the guard node IP is Unknown.
Snowflake log analysis
[edit]Optional.
1 Enable and view Snowflake log.
We can enable the snowflake log for debugging purposes by appending -log snowflake.log -log-to-state-dir to the ClientTransportPlugin snowflake... line in /usr/local/etc/torrc.d/50_user.conf.
2 We can view the snowflake log with:
sudo less /var/lib/tor/pt_state/snowflake.log
3 Tor data directory.
Note that we can always find the Tor DataDirectory with the following command:
anon-verify -v
DataDirectory /var/lib/tor
4 Done.
Snowflake log analysis steps have been documented.
Unsupported Pluggable Transport
[edit]WebTunnel
[edit]WebTunnel is an undocumented pluggable transport.
Rationale for Unsupported Bridges
[edit]Why are some pluggable transports unsupported? This is a technical explanation. Users are free to skip it.
The situation is similar to how it was for Snowflake for a long time![]()
. WebTunnel is unavailable from packages.debian.org. It is therefore difficult and maintenance time-intensive for Whonix to install WebTunnel in Whonix by default. Related: Default Application Policy.
Without volunteer development contributions to Whonix, this will probably take a few years, if it ever happens.
References:
- Adding WebTunnel Bridges to Whonix - Whonix Forum

- Introducing WebTunnel: Evading Censorship by Hiding in Plain Sight - Tor Project Blog

- WebTunnel Setup Guide - Tor Project

Warning: Bridged Networking
[edit]Note: While similar in name, there are two very different things.
- A) Bridges: These are used for censorship circumvention, to get around internet service provider (ISP) level network bans. Documented on this wiki page. See above from beginning of this wiki page.
- B) Bridged Networking: This is a virtualizer specific setting such as in VirtualBox that can in theory be changed on the host operating system.
Do not change VirtualBox settings on the host operating system for Whonix-Gateway's first or second network interface to a bridged network! This is unsupported, untested and should not be necessary. This is elaborated in wiki chapter Whonix-Gateway Security, Warning: Bridged Networking.
Troubleshooting
[edit]Check Tor Network Connection is Using a Tor Bridge
[edit]Concerned bridge users can complete a simple check.
1 Open Nyx as follows.
If you are using a graphical Whonix-Gateway, complete the following steps.
Start Menu → Applications → System → Nyx - Status Monitor for Tor
If you are using a terminal Whonix-Gateway, type.
nyx
If you are using Qubes-Whonix™, complete the following steps.
Qubes App Launcher (blue/grey "Q") → Whonix-Gateway™ ProxyVM (commonly named sys-whonix) → Nyx - Status Monitor for Tor
2 Use the right arrow button to navigate to page 2 of 5 in Nyx.
3 If a bridge is in use, the circuit information will be similar to this.
192.168.0.1 UNKNOWN 1 / Guard
4 If a bridge is not in use, the circuit information will be similar to this.
IP Nickname 1 / Guard
The IP is the real IP (not 192.168.0.1) of the Guard, and the Nickname is the name of that Guard relay.
5 Exit Nyx by pressing the following.
q q
6 Done.
The Tor bridge connection check is complete.
Connection Issues
[edit]After configuration, connection problems can relate to firewall settings that block outgoing connections to the ports provided by the bridge. To check the port the bridge is using, see the following example.
bridge 109.195.132.77:22321
In this example, the IP address is 109.195.132.77, while the the port is 22321.
Try using a (private) (obfuscated) bridge that uses port 80 or 443, as these ports are mostly used for web browsing and therefore usually unblocked.
Trying Packet Size and Timing Obfuscation for obfs4
[edit]If a provided obfs4 bridge does not work, the user can try enabling packet size and timing obfuscation by changing the iat-mode value in each last line to either 1 or 2. [21]
Better Connectivity without Real Censorship Circumvention
[edit]If a user is only concerned with connectivity (getting Whonix connected) and there is no need to attempt to Hide Tor use from the Internet Service Provider and/or local ISPs do not usually hinder connections to the public Tor network, then something simpler than Bridges can be tried.
The following setting only establishes Tor connections to public Tor network relays that listen on ports 80 and 443.
1 Edit the Tor configuration file.
Tor configuration file.
Open the file /usr/local/etc/torrc.d/50_user.conf in a text editor![]() of your choice with administrative rights.
of your choice with administrative rights.
1 Sysmaint notice.
Ensure the VM has administrative (sudo / root) access first. See also sysmaint.
2 Platform specific. Select your platform.
Graphical Whonix-Gateway SYSMAINT Session
If you are using a graphical Whonix-Gateway booted into PERSISTENT Mode | SYSMAINT Session, take the following step.
System Maintenance Panel → Open Terminal → run /usr/libexec/gateway-shortcuts/torrc
Graphical Whonix-Gateway Unrestricted Admin Mode
If you are using a graphical Whonix-Gateway and enabled unrestricted admin mode![]() , take the following step.
, take the following step.
Start Menu → System Tools → Tor User Config
If you are using Qubes-Whonix™, take the following step.
Qubes App Launcher (blue/grey "Q") → Service → Whonix-Gateway™ ProxyVM (commonly named sys-whonix) → Tor User Config
2 Add the following setting. [22]
FascistFirewall 1
3 Save the file and have the changes take effect.
Reload Tor.
After changing Tor configuration, Tor must be reloaded for changes to take effect.
Note: If Tor does not connect after completing all these steps, then a user mistake is the most likely explanation. Recheck /usr/local/etc/torrc.d/50_user.conf and repeat the steps outlined in the sections above. If Tor then connects successfully, all the necessary changes have been made.
If you are using Qubes-Whonix™, complete the following steps.
Qubes App Launcher (blue/grey "Q") → Service → Whonix-Gateway™ ProxyVM (commonly named 'sys-whonix') → Reload Tor
If you are using a graphical Whonix-Gateway, complete the following steps.
Start Menu → System Tools → Reload Tor
If you are using a terminal Whonix-Gateway, click
HERE for instructions.
Complete the following steps.
Reload Tor.
sudo systemctl reload tor@default.service
Check Tor's daemon status.
sudo systemctl status tor@default.service
It should include a a message saying.
Active: active (running) since ...
In case of issues, try the following debugging steps.
Check Tor's config.
sudo -u debian-tor tor --verify-config
The output should be similar to the following.
Sep 17 17:40:41.416 [notice] Read configuration file "/usr/local/etc/torrc.d/50_user.conf". Configuration was valid
4 Done.
The procedure is complete.
Missing ClientTransportPlugin Line
[edit]When a user has configured the following.
bridge obfs4 ...:... ... cert=... iat-mode=0
But forgot to add the corresponding line.
ClientTransportPlugin obfs4 exec /usr/bin/obfs4proxy
Then warnings will only be shown in logs.
[warn] We were supposed to connect to bridge '...:...' using pluggable transport 'obfs4', but we can't find a pluggable transport proxy supporting 'obfs4'. This can happen if you haven't provided a ClientTransportPlugin line, or if your pluggable transport proxy stopped running.
Missing ClientTransportPlugin Executable
[edit][warn] Could not launch managed proxy executable at '/usr/bin/obfs4proxy' ('No such file or directory').
Deprecated Tor Pluggable Transports
[edit]Scramblesuit
[edit]scramblesuit: Unrecommended (see footnote). Use the provided obfs4 instructions instead. [23]
Flashproxy
[edit]flashproxy: Unrecommended (see footnote). Use the provided obfs4 instructions instead. [24]
See Also
[edit]- Lantern: An alternative censorship circumvention tool documented for Qubes-Whonix™ only.
- Unfinished: Censorship Circumvention Tools other than bridges.
Appendix
[edit]Hosting Bridges
[edit]While most of this chapter is dedicated to bridge use, this section clarifies a few concepts about Tor Bridge hosting, although detailed how-to instructions are not provided. To help others you must reside in a country that does not censor Tor and have a reasonably fast connection. The VM or host in use should have port forwarding enabled to allow direct connections because all bridge server types require this, including Snowflake.
Volunteer Snowflake instances run proxies to the bridge and are not bridges themselves. These proxies can be run behind a NAT because clients use the built-in NAT punching properties of WebRTC to connect. The proxies then open a WebSocket connection to the Snowflake bridge and relay data between the WebRTC connection with the client and the bridge. The Snowflake bridges cannot run behind a NAT and are similar to all other existing pluggable transports in this regard. [25]
Using bridge users' traffic to mask your own onion service traffic is difficult to do properly. [26] This may be of questionable efficacy if traffic is not heavy and the bridge traffic of other pluggable transports is easily able to be excluded by advanced adversarial traffic analysis.
In order to implement a similar defense using a Snowflake proxy (as opposed to a bridge), a custom client needs to be written that would encapsulate your Tor traffic and send it through a TCP WebSocket connection to the Snowflake bridge. This measure is ineffective for the same reasons bridge cover traffic is not. For other traffic to provide effective cover, client traffic needs to be mixed with concurrent, relayed Tor relay traffic; this may require a relatively high speed main network relay to be in use frequently enough to help. Note that website fingerprinting of client traffic is not a severe enough threat to warrant this type of defense for clearnet-destined tor traffic, but it is helpful to protect against end-to-end correlation attacks. [27] [28]
Active Probing
[edit]Various jurisdictions utilize active probing in order to block circumvention proxies, including different versions of Tor and the detection and blocking of bridges. Perhaps the most infamous example is the probing system used by the "Great Firewall of China" (GFW). The Tor Project first began exploring this issue in October 2011![]()
. At that time it was discovered that:
[29]
...connections to US-based Tor bridge relays were being regularly cut off after a very short period of time. At the time we performed some basic experimentation and discovered that Chinese IPs (presumably at the behest of the Great Firewall of China, or GFW) would reach out to the US-based bridge and connect to it shortly after the Tor user in China connected, and, if successful, shortly thereafter the connection would be blocked by the GFW. There wasn't time for a detailed investigation and analysis at the time, but that kernel eventually grew into the investigation detailed below. We were, however, able to determine that limiting connections to the bridge relay to only the single IP expected to be its client would, in fact, block the probes and allow the connection to remain open for an extended period (>48 hours in our testing).
The Tor Project identified two types of probing: [29]
- Garbage binary probes: when an SSL connection took place, arbitrary binary data was sent to the non-China side of connections originating from China to TCP port 443 (HTTPS). Deep packet inspection (DPI)

was suspected because the probe occured soon after the connection was established. [30]
- Tor probes: China-based Tor clients connecting to US-based bridge relays were probed at 15 minute intervals. The bridge received probes from China-based hosts that: established a TCP connection, performed a SSL negotiation, followed by a SSL renogotiation and the building of a one-hop circuit (including a
BEGIN_DIRcell).
To prevent probing, Tor developers then responded by changing the list of supported SSL ciphers included in the "hello" packet sent to Tor clients in China. [31]
Further investigation of the GFW active probing system in 2015 revealed: [32]
- Bridges detected and blocked by the GFW remain blocked. However, a small window of opportunity was available around every 25 hours when Tor clients in China could connect to bridges.
- TCP headers of active probes suggest the thousands of IP addresses are controlled by a single source and not independent computers.
- The GFW also targets other circumvention systems like SoftEther and GoAgent. [33]
- Bridges are probed by the GFW using the standard Tor protocol, as well as obfs2/3.
- Tor probes had increased in frequency from 15 minute intervals to near real-time -- active probes emerged half a second after a bridge connection was established.
- The GFW sensor is unable to reassemble TCP streams.
In 2019, The Tor Project noted: [34]
When the Great Firewall's active probing attack discovered a bridge, the GFW used to block the bridge by its IP address and port, which conveniently left other transport protocols that ran on the same IP address, say obfs4, reachable. This behavior changed recently, and bridges are now blocked by their IP address. This means that a protocol that is vulnerable to the GFW’s active probing attack (e.g., vanilla Tor, fte, and obfs3) can get the entire bridge blocked—including obfs4, which is resistant to active probing! The new BridgeDB release addresses this issue by only handing out a bridge’s probing-resistant protocols if the bridge supports protocols that are both vulnerable and resistant to active probing. For example, if a bridge supports both vanilla Tor and obfs4, then we only hand obfs4 to users.
Research suggests ScrambleSuit![]()
and obfs4
![]()
can successfully defend against probing attacks, but their ongoing effectiveness will remain an open research question. The take-home message is that Whonix users in heavily censored nations like China and Iran will require an obfs4 bridge or other probe-resistant protocols to try and circumvent censorship.
For further reading on this topic, see:
- Examining How the Great Firewall Discovers Hidden Circumvention Servers

- The Great Firewall’s active probing circumvention technique with portknocking and SDN

- Demystifying the Great Firewall of China

- Analyzing China’s Blocking of Unpublished Tor Bridges

- How the Great Firewall of China is Blocking Tor

- Detecting Probe-resistant Proxies

Footnotes
[edit]- ↑ https://blog.torproject.org/different-ways-use-bridge

- ↑ Over time, censors have gotten better at detecting Tor network traffic between the client and the first hop, even with the use of more advanced pluggable transports. There is a cyber-censorship arms race in effect.
- ↑ Some bridge addresses are freely provided by the Tor website or by email upon request, meaning adversaries likely use these methods to obtain bridge information. The Tor Project has some protection against adversary threats, but they are far from perfect.
- ↑ Google sees forty percent of Tor Exits' DNS traffic and so using them as a bridge aids website fingerprinting attacks. That said, there is evidence that website fingerprinting is more difficult to mount than previously thought. See: The Effect of DNS on Tor’s Anonymity

- ↑
Tor manual: PublishServerDescriptor

Without this option set, The Tor Project can learn about the bridge and may distribute its address to others, potentially handing this information to an adversary seeking to generate a list of all known bridges.
- ↑
https://gitlab.torproject.org/legacy/trac/-/issues/18072

- ↑
This pluggable transport has been deprecated by The Tor Project in favor of obfs4, meek, Format-Transforming Encryption (FTE) and ScrambleSuit

.
- ↑
https://blog.torproject.org/recent-and-upcoming-developments-pluggable-transports#obfs2_deprecation

- ↑ https://2019.www.torproject.org/docs/bridges.html.en#PluggableTransports

- ↑ https://2019.www.torproject.org/docs/pluggable-transports.html.en

- ↑
The obfs4 protocol was developed and is in the process of being deployed by the Tor Project in response to the vulnerability of the obfs3 protocol to detection via active probing attacks. It is expected to supersede the obfs3 protocol as the front-line Pluggable Transport used by most Tor users.
- ↑ https://tb-manual.torproject.org/circumvention/

- ↑ Stop: sudo systemctl stop tor@default sudo systemctl disable tor@default Start: sudo systemctl enable tor@default sudo systemctl start tor@default
- ↑ Or Advanced Users would need to hardcode IP addressed rather than using hostnames.)
- ↑
Replace
10.0.2.3.- To identify the IP to substitute, execute the command below:
- qubesdb-read /qubes-netvm-primary-dns
- For example, the output might be:
10.139.1.1
- In this case, replace
10.0.2.3with10.139.1.1. Note: Use the actual IP from the output of thequbesdb-read /qubes-netvm-primary-dnscommand.
- ↑
https://gitlab.torproject.org/legacy/trac/-/wikis/doc/Snowflake

- ↑
The line starting with
ClientTransportPluginwas taken from the Tor Browser folder file.grep "ClientTransportPlugin snowflake" ~/.tb/tor-browser/Browser/TorBrowser/Data/Tor/torrc-defaultsWhat is the link to thetorrc-defaultsfile The Tor Project git? The path was adjusted from./TorBrowser/Tor/PluggableTransports/snowflake-clientto/usr/bin/snowflake-clientto be compatible with these instructions. The line starting withBridgewas taken from this command:~/tor-browser/Browser/TorBrowser/Data/Tor/torrc
It was previously:
Bridge snowflake 0.0.3.0:1 2B280B23E1107BB62ABFC40DDCC8824814F80A72
- ↑ Or Advanced Users would need to hardcode IP addressed rather than using hostnames.)
- ↑
Replace
10.0.2.3.- To identify the IP to substitute, execute the command below:
- qubesdb-read /qubes-netvm-primary-dns
- For example, the output might be:
10.139.1.1
- In this case, replace
10.0.2.3with10.139.1.1. Note: Use the actual IP from the output of thequbesdb-read /qubes-netvm-primary-dnscommand.
- ↑
AppArmor has appropriate permissions for Snowflake operation. /etc/apparmor.d/local/system_tor

already contains
/usr/bin/snowflake-client ix,. - ↑
1 = Enabled: ScrambleSuit-style with bulk throughput optimizations.
2 = Paranoid: Each IAT write will send a length sampled from the length distribution (expensive). See: https://lists.torproject.org/pipermail/tor-commits/2014-August/079402.html

- ↑
https://support.torproject.org/#tbb_tbb-firewall-ports

- ↑
Quote intrigeri

(Tails developer):
On tor-talk we've been told "You shouldn't prioritise ScrambleSuit because it is superseded by obfs4", and there are now pressing plans in the Tor Project to deprecate obfs2 and obfs3 in favour of obfs4. Hence rejecting this ticket, and focusing on #7980

[obfs4 support] instead.
Also see Tor Announcement under heading "obfs4 and scramblesuit"

- Old instructions: Deprecated#scramblesuit
- ↑
Flashproxy has been removed from Tor Browser

, therefore it can be considered deprecated.
- Old instructions: Deprecated#flashproxy
- ↑ https://gitlab.torproject.org/legacy/trac/-/wikis/doc/Snowflake

- ↑ https://github.com/mikeperry-tor/vanguards/blob/master/README_SECURITY.md#the-best-way-to-run-tor-relays-or-bridges-with-your-service

- ↑ https://lists.torproject.org/pipermail/tor-dev/2020-January/014127.html

- ↑ https://2019.www.torproject.org/docs/faq.html.en#BetterAnonymity

- ↑ 29.0 29.1 https://blog.torproject.org/knock-knock-knockin-bridges-doors

- ↑ At that time probing did not occur when the obfsproxy or plain-text protocols were used, presumably because a SSL handshake does not take place.
- ↑ They did note that ongoing Chinese censorship efforts would necessitate the development of new Tor protocols, handshakes and extensions over time, such as improved obfsproxy protocols.
- ↑ https://blog.torproject.org/learning-more-about-gfws-active-probing-system

- ↑ Suggesting the active probing system is modular in nature and can be configured to detect newer, proxy-based circumvention tools.
- ↑ https://blog.torproject.org/new-release-bridgedb-071

License
[edit]Whonix Bridges wiki page Copyright (C) Amnesia <amnesia at boum dot org>
Whonix Bridges wiki page Copyright (C) 2012 - 2026 ENCRYPTED SUPPORT LLC <adrelanos(at)whonix.org(Replace(at)with@.)Please DO NOT use e-mail for one of the following reasons: Private Contact: Please avoid e-mail whenever possible. (Private Communications Policy) User Support Questions: No. (See Support.) Leaks Submissions: No. (No Leaks Policy) Sponsored posts: No. Paid links: No. SEO reviews: No. Advertisement deals: No. Default application installation: No. (Default Application Policy) >This program comes with ABSOLUTELY NO WARRANTY; for details see the wiki source code.
This is free software, and you are welcome to redistribute it under certain conditions; see the wiki source code for details.

We believe security software like Whonix needs to remain Open Source and independent. Would you help sustain and grow the project? Learn more about our 14 year success story and maybe DONATE!