Whonix - Superior Internet Privacy
Is Whonix safer than VPNs?
| Whonix | VPNs | |
|---|---|---|
| Hidden IP address (basic) Your IP address acts as a global unique identifier which is linked to your real identity. Any website or server you are connecting to knows your IP address. Most Internet Service Providers (ISPs) keep a log of IP addresses assigned to you and when you used them. The IP address reveals your approximate physical location to any destination you connect to. | ||
|
Hidden Identity
Even if your IP is hidden trackers can use "Fingerprinting" techniques to identify you.
Hiding your identity is harder than just hiding your IP! Whonix protects from browser fingerprinting, and website traffic fingerprinting. |
||
|
No Logging
Whonix cannot log user IP addresses or activity. This is due to a
fundamental architecture design
decision to keep maximum user privacy.
Most VPNs have a policy of not storing any user data. But if they were forced to do so they could start storing user data easily. |
|
|
|
Leak Shield
Even if a connection is tunneled it can be hijacked inside the browser. One leaky connection
already compromises the user's anonymity.
Whonix has a watertight leak shield.
Some VPN providers also have a fail-closed mechanism however the quality varies very much and fails against malware. |
||
|
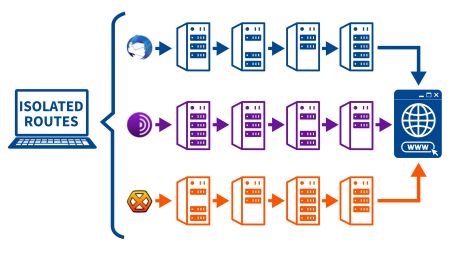
Server Relays avg.
The servers used for tunneling MUST NOT know the user. This is only possible if there are
multiple
and
independent servers
as relays on a
strict need-to-know basis
and
onion-layered encryption.
Some VPN providers provide double VPN but it’s still the same provider and lacks distributed trust by design. |
3 | 1 |
|
Virus / Malware Protection
A
malware (virus)
free system
is crucial
because a lot malware is stealing the user's data and identity.
Whonix is based on Kicksecure, a hardened, well documented Linux so the user is already safer.
Some VPN subscriptions contain anti-malware scanners but their capability is limited . A better approach is to prevent any malware from entering the system through security hardening and knowledge. |
|
|
| Keyboard Typing Cloak Trackers can identify their targets by their keyboard typing style. Whonix prevents this kind of attack. |
|
|
| Timestamp Attack Protection Trackers can identify their targets by minimal divergence from the standard time in the network requests called time attacks. Whonix prevents this kind of attack. |
|
|
| App Stream Isolation In Whonix distinct pre-installed applications are routed through different network paths for maximum security. |
|
|
| Open Source / Freedom Whonix has a full dedication to Open Source and Freedom Software. Only some VPNs have open source elements and even less are fully Open Source. |
|
|
| Pricing |
FREE or Donation |
$5 - $20 per month |
|
Download Whonix now! |
Learn More: Whonix versus VPNs
Trusted by Security Experts

For the even more paranoid, there is a lesser-known Tor-enabled OS called Whonix
I use Qubes and a Whonix gateway literally everyday

Whonix adds a layer of anonymity to your business tasks.

Whonix is about as anonymous as an OS can get before it all becomes too inconvenient for normal use.

All of our staff are aware, for anything privacy critical, Whonix is our go-to solution. Anybody who takes privacy serious should have a Whonix VM at least.

Whonix, an operating system you can run in a virtual machine to maximize your online anonymity; it’s ideal for maintaining a secret identity.
Watertight Privacy Architecture
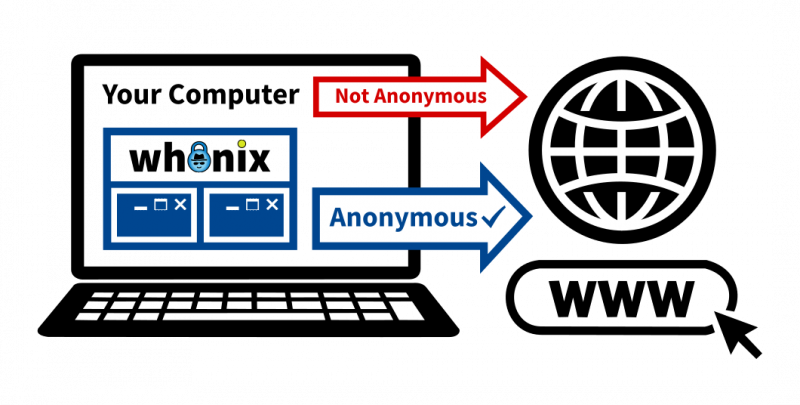
Whonix handles all your activity in a virtual machine, forcing all Internet traffic through the Tor network, providing reliable IP hiding and the strongest protection for your IP address.
Fully Featured with Advanced Security Components

Elite Spy Defense
Hiding your identity is harder than just hiding your IP. Whonix provides a full spectrum anti-tracking protection.

Maximum Anonymity
Whonix provides maximum anonymity by design by utilizing the best privacy technologies and research.

12 Years of Success
For over 12 years we have successfully protected our users from everyday trackers and even from high level attacks. And we're just getting started!

Cyber Security Best Practices
You can't be anonymous without being secure. Security hardened operating system Kicksecure is the core of Whonix.

Bulletproof IP protection
Whonix has powerful protection measures against trackers, malware and many more attack vectors to get your IP address.

Cloaking your typing style
Your typing behavior can be used to identify you. Whonix prevents this with a cloak for your keystrokes.
Applications that are reviewed and pre-configured in Whonix
Freedom Values

Open Source
We respect user rights to review, scrutinize, modify, and redistribute Whonix. This improves security and privacy for everyone.
Freedom Software
Whonix is Freedom Software and contains software developed by the Free Software Foundation and the GNU Project.
Research and Implementation Project
Whonix is an actively maintained research project making constant improvements; no shortcomings are ever hidden from users.

Fully Auditable
Whonix is independently verifiable by security experts and software developers around the world. This improves security and privacy for everyone.

Complete respect for privacy and user freedom
Whonix respects data privacy principles. We don’t make advertising deals or collect sensitive personal data.
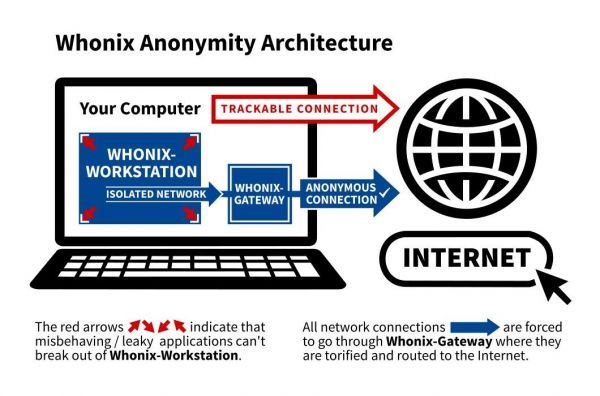
Your IP gives away your identity. Cloaking your IP address is difficult because the Internet is not designed for privacy. Whonix solves this problem by forcing all connections through multiple anonymity servers with its Dual-VM Architecture .
DNS leaks are impossible with Whonix. And even malware with root privileges cannot discover the user's real IP address. Whonix was thoroughly leak tested through corridor (Tor traffic whitelisting gateway) and other leak tests.
Internet tracking companies don't even need to know your IP address to be able to identify you. They use so-called Browser Fingerprinting which can track you even better than an IP address.
Even your personal typing style or your individual computer time can give away your identity. Every website has a unique fingerprint so your Internet history is not even safe with a VPN.

Our website offers an onion service option, enhancing user anonymity through alternative end-to-end encryption that avoids dependence on flawed TLS certificate authorities flawed TLS certificate authorities and the mainstream Domain Name System (DNS).

Whonix utilizes Tor, the best anonymity network, which provides an open and distributed relay network to defend against network surveillance.
Multiple server hops. Privacy by design. Need to know architecture. Onion-layered encryption. Unlike Virtual Private Networks (VPN), Tor provides anonymity by design and removes trust from the equation.

Decades of research by the security community lead to many best practices. Whonix is based on Kicksecure which is a security-hardened Linux distribution that implements the consensus of these reasonable security measures.

Your typing style can be used to track you. To prevent this, Whonix comes with kloak (a keystroke anonymizer) installed by default
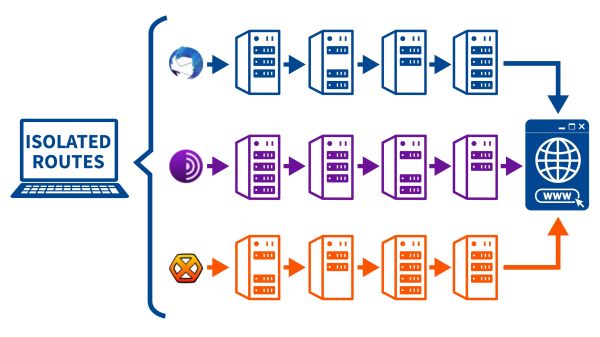
Distinct applications are routed through different paths in the Tor network. This is called Stream Isolation.

Timing-based fingerprinting attacks on Whonix users are mitigated through Boot Clock Randomization and secure network time synchronization via sdwdate (Secure Distributed Web Date).

Mouse tracking allows websites to collect detailed behavioral data—such as click patterns and cursor paths—that can be analyzed with AI to identify users across sessions and even across different networks. Whonix includes tools like Kloak and Qubes Event Buffering to disrupt these tracking methods by adding subtle randomness to user input.

Not even WE know. Whonix has a strong organisational separation which means: Even we do not have access to IP connection logs!

The Everything Tor OS. All internet traffic is routed through the Tor anonymity network. No exceptions. Whonix is the "All Tor Operating System".
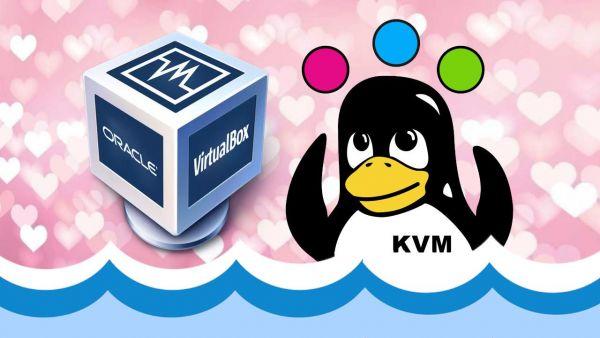
Virtualizer Friendly. Since Whonix runs in a virtualizer it provides an abstraction layer from the host operating system. This hides hardware serial numbers and prevents host file leaks.

Anonymously hosting a web server such as nginx (or any other type) is extremely difficult. Location / IP hidden servers are usually hosted using Tor onion services. The disadvantage is, that these are only reachable for users of Tor (such as Tor Browser or Whonix users). With Whonix, it's possible to host a location / IP hidden server service while it's reachable over clearnet . A very little known, but very unique and powerful feature.

Learn more about our anonymity, privacy and security settings pre-configuration anon-apps-config .

Anonymity thrives on awareness: Dive into Whonix' detailed documentation and guides to learn how to safeguard your identity and maintain privacy across all your activities.

Our vibrant Whonix community features Forums, Contributors and RSS

Tor Browser is optimized for anonymity and millions of daily users help you blend in with the crowd. Tor Browser provides protection from browser fingerprinting.
Tor Browser is the only serious and actively developed browser designed and recommended for anonymity.
The browser is fully featured because it is based on the modern and popular Mozilla Firefox browser, Visit any destination including modern websites such as YouTube.

Prevent de-anonymization of Tor onion services via utilization of the Tirdad kernel module for random ISN generation .
tor-ctrl-observer shows connection information of applications using Tor.

Whonix has over 12 years of success. We have successfully protected our users from everyday trackers and even from high level attacks . With the next decade in mind, we are constantly improving Whonix' privacy and security.

All the Whonix source code is licensed under OSI Approved Licenses. We respect user rights to review, scrutinize, modify, and redistribute Whonix. This improves security and privacy for everyone.
Whonix is Freedom Software and contains software developed by the Free Software Foundation and the GNU Project.
Research and Implementation Project: Whonix makes modest claims and is wary of overconfidence. Whonix is an actively maintained research project making constant improvements; no shortcomings are ever hidden from users.

Whonix is independently verifiable by security experts and software developers around the world; you don’t have to trust developer claims. This improves security and privacy for everyone.

Whonix respects data privacy principles. We don’t make advertising deals or collect sensitive personal data. There are no artificial restrictions imposed on possible system configurations .

We believe security software like Whonix needs to remain open source and independent. Would you help sustain and grow the project? Learn more about our 13 year success story and maybe DONATE!