Stream Isolation
Prevent Identity Correlation through Circuit Sharing by using Tor Stream Isolation.

Introduction
[edit]Essentials
[edit]- No common term without Tor: If the internet is used normally, without Tor, a proxy, or VPN, there is no widely used term for this. This could be coined "connecting over clearnet".
- Tor Browser on the host is application-limited: When using Tor without Whonix such as when using the Tor Browser Bundle on a host operating system such as Windows or Debian, only the Tor Browser Bundle connects over Tor. All other applications are still using clearnet.
- Whonix torifies system traffic via the gateway: In case of Whonix: All traffic originating from Whonix-Workstation™ and Whonix-Gateway™ is routed to the Tor software.
For technical details, click on "Learn More" on the right side.
- Traffic from Whonix-Gateway also routed over Tor: Starting from Whonix version
0.2.1, traffic from Whonix-Gateway is also routed over Tor. This approach conceals the use of Whonix from entities monitoring the network. - Gateway's own traffic not essential for anonymity: To preserve the anonymity of a user's Whonix-Workstation activities, it is not essential to route Whonix-Gateway's own traffic through Tor. (Note: The gateway is mainly a tool that helps route traffic; it does not typically contain personal activity data.)
- DNS configuration on Whonix-Gateway has limited impact: Altering DNS settings on Whonix-Gateway in
/etc/resolv.confonly impacts DNS requests made by Whonix-Gateway's applications that utilize the system's default DNS resolver. (DNS is like the internet's phonebook - it translates website names to IP addresses.) By default, no applications on Whonix-Gateway that generate network traffic use this default resolver. All default applications on Whonix-Gateway that produce network traffic (like apt, systemcheck
, sdwdate) are explicitly configured, or forced by uwt wrappers, to use their dedicated Tor
SocksPort(refer to Stream Isolation). - Whonix-Workstation DNS requests handled via Tor: Whonix-Workstation's default applications are configured to use dedicated Tor
SocksPorts(see Stream Isolation), avoiding the system's default DNS resolver. Any applications in Whonix-Workstation not set up for stream isolation - such asnslookup- will use the default DNS server configured in Whonix-Workstation (through/etc/network/interfaces), which points to Whonix-Gateway. These DNS requests are then redirected to Tor'sDnsPortby the Whonix-Gateway firewall. (This ensures DNS lookups still go through Tor even if they use the default method.) Changes in Whonix-Gateway's/etc/resolv.confdo not influence Whonix-Workstation's DNS queries. - Tor process traffic allowed direct internet access: Traffic produced by the Tor process, which by Debian's default operates under the account
debian-torand originates from Whonix-Gateway, can access the internet directly. This is permitted because the Linux user accountdebian-toris exempted in the Whonix-Gateway Firewall and allowed to use the "regular" internet. (This is necessary for Tor to establish its connections.) - Tor mostly uses TCP traffic: As of Tor version
0.4.5.6(with no changes announced at the time of writing), the Tor software predominantly relies on TCP traffic. (TCP is a common protocol used for stable internet connections.) For further details, see Tor wiki page, chapter UDP. For DNS, please refer to the next footnote. - Tor's DNS independence and exceptions: Tor does not depend on, nor use, a functional (system) DNS for most of its operations. IP addresses of Tor directory authorities are hardcoded in the Tor software by Tor developers. (That means Tor knows important addresses in advance and doesn't need to look them up.) Exceptions include:
- Proxy with domain name: Proxy settings that use proxies with domain names instead of IP addresses.
- Pluggable transport domain resolution: Some Tor pluggable transports, such as meek lite, which resolve domains set in
url=andfront=to IP addresses, or snowflake's-front.
- Two distinct issues: There are two different issues.
- IP Hiding: Whonix provides Reliable IP Hiding in any case irrespective of applications (such as browsers, ssh, Remmina), activities (such as Remote Administration), or protocols such as TCP, DNS, ICMP, UDP, RDP). Using helper utilities such as
torsocks,torifyor configurations such as TorSocksPorts is not required for IP concealment. In context of anonymity, hiding of IP addresses is of absolutely crucial importance. - Stream Isolation: Provides additional privacy protection by preventing correlation between different applications' traffic. Stream isolation aware applications; using helper utilities such as
torsocks; and/or configurations such as TorSocksPortare required. Some are already pre-configured. Compared to IP hiding, stream isolation is a detail optimization precaution but not of critical importance.
- IP Hiding: Whonix provides Reliable IP Hiding in any case irrespective of applications (such as browsers, ssh, Remmina), activities (such as Remote Administration), or protocols such as TCP, DNS, ICMP, UDP, RDP). Using helper utilities such as
Transparent Proxy
[edit]This chapter explains what a Transparent Proxy is. It is required knowledge in order to understand the following chapters.
Terminology:
- Meaning of transparent proxying: Transparent proxying means, simplified and unspecific to Whonix:
An application can connect without requiring additional configuration.
- Clearnet Firefox on the host: Use Firefox on host operating system without Tor or any proxy/VPN without Whonix involved: It is not clear this should be called "transparent proxying". It is probably best not to call it that way to avoid confusion. In that case, the home router is likely doing "transparent proxying". A proxy that is transparent. It does things for the user/program without the user necessarily having to know anything about it.
- Tor Browser on the host: Using Tor Browser on the host without Whonix involved: This is an example of "no transparent proxying available". [1]
- Other transparent proxy types exist: There are also other types of transparent proxies such as content filtering, virus scanning, and so on.
- Whonix specific meaning: More complex, specific to Whonix:
An application can use TCP/DNS [UDP blocked] over Tor (user -> Tor -> destination) without requiring additional configuration.
Whonix specific:
- Enabled by default: Whonix has the feature
transparent proxyingenabled by default.transparent proxyingis a feature that most users want. Not enablingtransparent proxyingby default would be confusing for most users. - Whonix-Gateway acts as a Tor Transparent Proxy: In other words, Whonix-Gateway by default can be used as a Tor Transparent Proxy. Connections from Whonix-Workstation™ to Whonix-Gateway are transparently proxied through Tor.
- Example application: For example if using Telegram in Whonix: Uses transparent proxying because it is not pre-configured by default to use Tor proxy settings.
Identity Correlation through Tor Circuit Sharing
[edit]- Risk from circuit sharing: If the user installs custom applications and omits explicitly taking precautions against identity correlation through Tor circuit sharing, the user is risking that different activities, let's say web (Chromium or similar) or IRC (HexChat or similar) go through the same Tor circuit and Tor exit relay.
- What an observer can still correlate: Even though the user would still be anonymous, i.e. the Tor exit relay would still not know the user's real IP/location, the Tor exit relay (and maybe the the Tor exit relay's internet service provider (ISP)) can potentially correlate those activities from different applications to the same pseudonym.
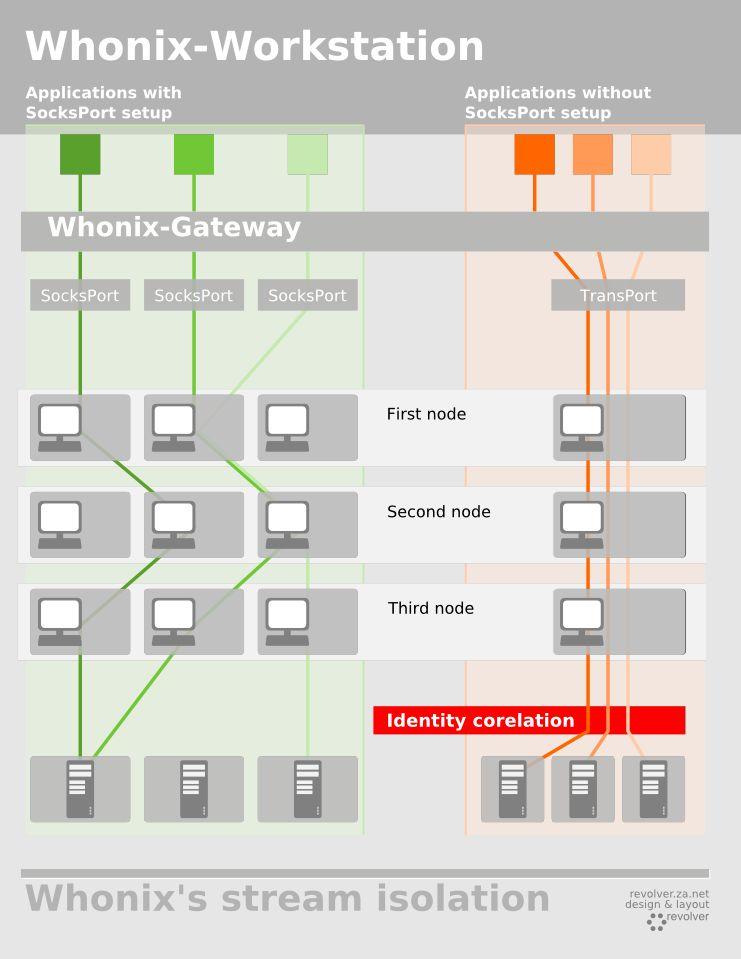
SocksPortvsTransPortbehavior: The following graphic illustrates the difference of using TorSocksPorts compared to using Tor'sTransPort.- Dedicated
SocksPortper application: Using a dedicated TorSocksPortper application results in taking different routes through the Tor network per application. - Relay changes vary: Not necessarily all Tor relays (first, second, third) get replaced. Sometimes just the first, sometimes just the second, sometimes just the third, and sometimes multiple Tor relays in the Tor circuit change.
- Dedicated
- Different circuit does not guarantee different exit: Stream isolation does not necessarily result in using a different Tor Entry Guard or Tor exit relay. Therefore, a different Tor circuit can likely lead to using a different Tor exit relay and IP Address, but this is not guaranteed. Related: Only Use One Online Pseudonym at the Same Time
Figure: Stream Isolation Illustration
- Whonix protection and why technical background knowledge helps: Whonix implements protection against identity correlation through Tor circuit sharing for preinstalled applications, however, for better privacy, the user is advised to understand a bit of the technical background.
- How isolation is achieved: Different
SocksPorts,DnsPorts, orTransPorts are routed through different Tor circuits, therefore preventing identity correlation. - Default application configuration: Whonix configures most applications that come preinstalled with Whonix to use a different
SocksPort, thus no identity correlation is at risk. - How applications are directed to different
SocksPorts: Whonix uses either socks proxy settings to direct various applications to differentSocksPorts or uwt
(more information below).
/etc/hostsand stream isolation: Applications configured for stream isolation (those using aSocksPort) ignore the/etc/hostsfile. This includes for example Tor Browser. Therefore modifications to/etc/hostsfor the purpose of adblocking are futile (unless using Tor Browser Transparent Proxying). Related: Tor Browser Filtering/etc/hostsand transparent proxying: Applications not configured for stream isolation, i.e. those using transparent proxying are usually honoring the/etc/hostsfile. Select applications might have a specific implementation to ignore it depending on the application and unspecific to Whonix.- Other traffic defaults: Any other traffic (i.e. custom installed applications, misc applications, such as
nslookup, goes through Tor'sDnsPort, and/orTransPort(can be optionally disabled, see below).
List
[edit]Related:
- Whonix Default Application Policy
- Should strict stream isolation by a requirement in Whonix's Default Application Policy?

Applications in Whonix that are either prepared or fully pre-configured to prevent identity correlation through Tor circuit sharing:
By Settings
[edit]| application | pre-installed | pre-configured | stream isolation by method | port | comments |
|---|---|---|---|---|---|
| Tor Browser | Yes | Yes | socks proxy settings | 9150 [2] | - |
| Mozilla Thunderbird | Yes | Yes | socks proxy settings | 9102 | - |
| Instant Messenger | No | No | socks proxy settings | port prepared, IP 10.152.152.10, port 9103 | Chat |
| sdwdate | Yes | Yes | socks proxy settings | 9108 | Dev/TimeSync |
| systemcheck |
Yes | Yes | socks proxy settings | 9110 | - |
| Bitcoin electrum Wallet (BTC) | Yes | No (TODO |
socks proxy settings | port prepared, IP 10.152.152.10, port 9111 | - |
| Monero (XMR) | Yes | No (TODO) | socks proxy settings | - | - |
| Tor Browser Downloader by Whonix | Yes | Yes | socks proxy settings | 9115 | - |
| KDE application wide proxy settings | No | Yes [3] | socks proxy settings | 9122 no KDE applications with network activity pre-installed | - |
By uwt wrapper
[edit]| application | pre-installed | pre-configured | stream isolation by method | port | comments |
|---|---|---|---|---|---|
| apt-get | yes | yes | uwt wrapper | - | Update |
| aptitude | yes | yes | uwt wrapper | - | - |
| gpg | yes | yes | uwt wrapper | - | - |
| ssh | yes | yes | uwt wrapper | - | - |
| git | no | yes | uwt wrapper | - | - |
| wget | yes | yes | uwt wrapper | - | - |
| curl | yes | yes | uwt wrapper | - | - |
| scurl | yes | yes | uwt wrapper | - | Uses curl, therefore same as curl. |
none
[edit]| application | pre-installed | pre-configured | stream isolation by method | port | instructions |
|---|---|---|---|---|---|
| GNOME application wide proxy settings | no | no | none | no GNOME applications with network activity pre-installed | - |
systemcheck
|
yes | no [4] | none | See footnote. [4] | - |
Details
[edit]- How stream isolation is implemented: The required socks proxy settings are set up by various Whonix configuration packages or uwt wrappers, which are set up on Whonix-Gateway™ and on Whonix-Workstation.
- What uwt is: uwt is a wrapper around torsocks

, which is also already installed to /usr/bin/uwt.
- How uwt wrappers behave by default: For example, each time you run a uwt wrapped application, i.e. simply type apt-get in console, the uwt wrapper /usr/bin/apt-get will run. It adds uwt before apt-get. For curiosity, check nano /usr/bin/apt-get. Essentially, the uwt wrapper then runs /usr/bin/uwt /usr/bin/apt-get.anondist-orig. That is also the case for all other uwt wrapped applications.
- How to bypass uwt when needed: If you ever want or need to run a uwt wrapped application without uwt, do not run for example apt-get in console, instead run apt-get.anondist-orig. Use cases could be if you want to connect to localhost. If you know what you are doing, you should also be able to deactivate any uwt wrappers you dislike, see #Deactivate_uwt_Stream_Isolation_Wrapper.
- What bypassing uwt changes: When running /usr/bin/apt-get.anondist-orig, it directly goes through Tor's
DnsPortand through Tor'sTransPortand not through its ownSocksPort. - Automatic localhost passthrough behavior: uwt checks whether the command contains the words localhost or 127.0.0.1. If that is the case, uwt will not be used. The command will be run without uwt. Thus, if a localhost connection is falsely detected, it will leak, but only through Tor's
DnsPortand through Tor'sTransPort, which should be acceptable. - Isolate by destination address: Let's assume SSH goes over port 22 and you want to connect to different SSH servers and do not want an observer to be able to correlate that activity to the same pseudonym. If the SSH servers run on different IPs, isolate by destination address might help.
- Isolate by destination port: This doesn't seem to be useful for anything in Whonix. Applications using different protocols (and therefore different ports) are already isolated through using different
SocksPorts. - Why it doesn't help for web browsing: Isolate by destination port doesn't really achieve anything for web browsing: tor-talk Tor's stream isolation features defaults

.
- Where to learn more: For more information about stream isolation refer to the Tor manual.
- Stable manual: Tor stable manual

- Alpha manual: Tor alpha manual

- Stable manual: Tor stable manual
Tor Browser
[edit]- Domain-based SOCKS authentication: Tor Browser has a feature Tor Browser should set SOCKS username for a request based on first party domain

. Tor Browser makes use of Tor's
IsolateSOCKSAuthoption. Whonix does not break this feature. [5] - Note about a previous claim: This wiki page stated
Different tabs and websites in Tor Browser are isolated by Tor Browser. [6]. This was either always incorrect or Tor Browser's behavior has changed meanwhile.
Tor circuit and HTTP connection linkability
Design Goal: Tor circuits and HTTP connections from a third party in one URL bar origin MUST NOT be reused for that same third party in another URL bar origin.
Implementation Status: The isolation functionality is provided by a Torbutton component that sets the SOCKS username and password for each request
. The Tor client has logic to prevent connections with different SOCKS usernames and passwords from using the same Tor circuit. Firefox has existing logic to ensure that connections with SOCKS proxies do not re-use existing HTTP Keep-Alive connections unless the proxy settings match. We extended this logic
to cover SOCKS username and password authentication, providing us with HTTP Keep-Alive unlinkability.
While the vast majority of web requests adheres to the circuit and connection unlinkability requirement there are still corner cases we need to treat separately
or that lack a fix altogether
.upstream, The Tor Project: The Design and Implementation of the Tor Browser (DRAFT)
- Upstream is the source of truth: Tor Browser is developed by upstream, The Tor Project

, which is an independent entity. For up-to-date information, refer to upstream, Tor Browser.
- Related forum discussion: https://forums.whonix.org/t/tor-browser-new-identity-differs-from-restarting-tor-browser-in-whonix/3098/4

Onion Services
[edit]- Automatic isolation for different onion services: Connections to different Tor Onion Services are automatically stream isolated. [7]
How to mitigate identity correlation
[edit]Scope, Responsibilities, and User Expectations
[edit]Whonix provides a Tor-routed platform, not perfect application-specific stream isolation for all third-party applications.
- What Whonix does: Whonix provides Reliable IP Hiding by default, transparent proxying, and stream isolation for many preinstalled applications.
- User advice:
- Prefer applications with built-in Tor support: If an application comes with native Tor support, also referred to as "Tor friendly applications", that is often preferable. Application developers interested in supporting Tor and anonymity are in a better position to implement fine-grained stream isolation.
- When using applications without built-in Tor support:
- If Advanced Users install custom applications without native Tor support and want to reduce the risk of identity correlation through Tor circuit sharing, then those applications usually require manual configuration, such as application-specific proxy settings or a socksifier such as
torsocks.- Use a dedicated Tor
SocksPortwhen possible: Different applications should generally use different TorSocksPorts. - Use a socksifier only when needed: A socksifier such as
torsockscan be useful for some applications, but behavior is application specific.
- Use a dedicated Tor
- If Advanced Users install custom applications without native Tor support and want to reduce the risk of identity correlation through Tor circuit sharing, then those applications usually require manual configuration, such as application-specific proxy settings or a socksifier such as
- For stronger assurance: Disable transparent proxying and test whether the application still works only through the intended Tor
SocksPort. - For application-specific details: Consult upstream application documentation and upstream developers.
- What Whonix developers generally cannot do: Whonix developers generally cannot continuously develop, verify, leak test, and maintain perfect stream isolation instructions for every third-party application and every future application version.
- What application developers should do: Application developers are best positioned to implement proper Tor support, such as native proxy settings, safe remote DNS behavior, and stream isolation aware integration.
- What Tor Project developers are responsible for: Tor Project documentation and Tor developer guidance are the source of truth for Tor stream isolation features, Tor client behavior, and Tor network best practices.
Tor friendly applications versus Applications without native Tor support
[edit]Choose the tab that best matches the application.
Tor friendly applications
Applications with built-in Tor support are generally preferable. These applications are in a better position to implement fine-grained stream isolation and other Tor-specific behaviors.
Technical guidance:
- Prefer applications with built-in Tor support: If an application comes with native Tor support, that is often preferable.
- Why this is preferable: Application developers interested in supporting Tor and anonymity are in a better position to implement fine-grained stream isolation.
- Use native application support: Use the application's native proxy settings or other upstream Tor integration as documented by upstream.
- For application-specific details: Consult upstream application documentation and upstream developers.
- Use of a dedicated Tor
SocksPortis usually unnecessary: Tor friendly applications should be using IsolateSOCKSAuth. In that case, a dedicated TorSocksPortis usually unnecessary. [8]
Applications without native Tor support
Applications without native Tor support usually require manual user configuration. In this case, Whonix can provide the platform and general guidance, but application-specific correctness depends on the specific application and its behavior.
Support and responsibilities:
- The legacy approach is less actively maintained: The legacy approach of torification of arbitrary applications seems to have been largely given up. There are very few edits to the Torify HOWTO

over the years. Nowadays some application developers are providing Tor-safe by default applications, i.e. applications designed for use with Tor in mind and not as an afterthought. Examples include Tor Browser and OnionShare. Also if users are asking how to torify specific applications and make sure these are leak free, users are probably told "use Whonix".
- Up to date torification instructions are difficult to maintain: Finding up to date instructions for torification is difficult because developing instructions for torification itself is a difficult process. Someone who understands networking needs to leak test whether the torification instructions are actually working. A leak would mean that portions of the application's traffic ignore proxy settings and/or circumvent the proxifier and are actually making external connections without using Tor. Such leaks would be much less severe in Whonix. It would only result in identity correlation through Tor circuit sharing but not in a leak of the user's real IP address to the destination.
- Support requests are usually ineffective: Asking for torification instructions for specific applications at Whonix Free Support is probably futile. Whonix can document the platform and general stream isolation model, but application-specific stream isolation is usually the responsibility of the upstream application developers. One of the main reasons for the inception of Whonix was that finding, developing and applying torification instructions is so difficult and one never really knows if it is 100% free of leaks. Even seriously reviewed torification instructions for one application would only apply to the exact version that was being reviewed. Not to future versions of the application.
- What Whonix developers do not generally do: Maintain perfect, current stream isolation instructions for every third-party application. Application behavior changes over time, and developing correct guidance requires application-specific review and leak testing.
Technical guidance:
- Manually configure custom applications: If you install custom software on Whonix-Workstation that uses the internet, and you want to prevent identity correlation through Tor circuit sharing (which you should do), you have to manually configure it. This is not a Whonix specific problem. [9] Read also Software installation on Whonix-Workstation.
- Use a dedicated
SocksPortper custom application: To protect against this, you have to set up and configure applications to use a dedicated TorSocksPort. Each custom installed application has to be directed to a dedicated TorSocksPort. For instructions how to do that, use the Torify HOWTO
. Generally, this can be done either by configuring the application's proxy settings or by using a proxifier (socksifier) such as
torsocks. - Use a socksifier only when needed: A socksifier such as
torsockscan be useful for some applications, but behavior is application specific. - Do not share a
SocksPortacross applications: If you redirect more than one application to the sameSocksPort, identity correlation is at risk. - Pre-prepared custom socks ports exist: On Whonix-Gateway there are already a lot of custom socks ports prepared for use with custom installed applications. [10]
- Default range without isolation flags: Without IsolateDestAddr and without IsolateDestPort:
SocksPort9153to9159 - Range with destination address isolation: With IsolateDestAddr, but without IsolateDestPort:
SocksPort9160to9169 - Range with destination port isolation: Without IsolateDestAddr, but with IsolateDestPort:
SocksPort:9170to9179 - Range with both isolation flags: With IsolateDestAddr and with IsolateDestPort:
SocksPort:9180to9189 - Add more if needed: If those are not enough, you can add your own.
- Default range without isolation flags: Without IsolateDestAddr and without IsolateDestPort:
- Isolation flags are usually unnecessary: What are IsolateDestAddr and IsolateDestPort? You can learn about them in the Tor manual

. See also tor-talk mailing list: Tor's stream isolation features defaults

. Usually, unless you know better, you are better off not using IsolateDestAddr or IsolateDestPort.
- For stronger assurance: Disable transparent proxying and test whether the application still works only through the intended Tor
SocksPort. - No universal best method exists: What is better, configure the application's proxy settings or use a proxifier? There can be no generalized answer as this is highly application specific. The most comprehensive documentation of this is the Torify HOWTO

. Also, a web search can be performed on how to torify applications.
Basic Protection
[edit]- Use the pre-configured list where possible: A #list of applications that come pre-installed with Whonix are pre-configured to prevent identity correlation through circuit sharing.
- Be aware of
TransPortpollution during tests: Traffic going throughTransPortby default includes systemcheck
when manually testing the
TransPortby usingsystemcheck --leak-tests. If that is of concern to you, see the following bullets. - Optionally adjust systemcheck behavior: It can be disabled in systemcheck, see prevent polluting
TransPort
, but that might make little sense.
- Prefer to avoid the test instead: Better to avoid the test instead.
- Understand the default routing: All custom installed applications' TCP traffic is routed through Tor's
TransPortand all their DNS requests through Tor'sDnsPort. This means different activities or "identities" in different applications (say browser, IRC, email) end up being routed through the same Tor circuit, thus identity correlation is at risk. [11] - Multiple Workstations are automatically separated: Multiple Whonix-Workstation are automatically stream isolated. [12]
- This adds stream isolation on top of torification: Applications inside Whonix are already torified but by applying these instructions inside Whonix the user would go one step further, i.e. add stream isolation.
- Honor protocol warnings: Protocol related warnings that you must honor still apply. You are still better off with Whonix, as it offers best possible Protocol-Leak-Protection and Fingerprinting-Protection.
- IP leak protection always applies: Whonix setup provides protection against IP leaks through protocol leaks

.
- Misconfiguration has predictable outcomes: No connections will be possible or traffic will continue going through Tor's
TransPortunless you disable transparent torification. - DNS warnings still matter: DNS related warnings

still apply, though to a lesser extent. An attack could only make correlations but still could not figure out your IP. To prevent that, see chapter better protection.
- Avoid local DNS resolvers: Do not use a local DNS resolver

, as all DNS requests would be executed by the same Tor circuit.
- Some leak classes do not apply here: Other leaks, such as applications not honoring the proxy settings / wrapper, ICMP or UDP leaks do not apply to Whonix.
SafeSocksis optional: The SafeSocks setting is for rejecting unsafe variants of socks that might cause DNS leaks. The Whonix design model mitigates DNS leaks by redirecting all requests to Tor'sDnsPort. Enabling this setting would give marginal benefit in this situation but would complicate debugging.
Generic instructions for configuring custom installed applications for stream isolation for less than 7 custom applications
- Install custom application.
- Configure application to use a dedicated Tor
SocksPortaccording to Torify HOWTO
by either configuring the application's proxy settings or by using a proxifier such as
torsocks. - Start custom application.
Generic instructions for configuring custom installed applications for stream isolation using proxifier (socksifier) torsocks
- Install custom application.
- Open a terminal.
Select your platform.
Non-Qubes-Whonix USER Session
If you are using a graphical Whonix with LXQt, complete the following steps.
Start menu → System Tools → QTerminal
Non-Qubes-Whonix SYSMAINT Session
In the System Maintenance Panel, under the Misc section, click Open Terminal.
Qubes-Whonix
If you are using Qubes-Whonix, complete the following steps.
Qubes App Launcher (blue/grey "Q") → Whonix-Workstation™ App Qube (commonly named anon-whonix) → QTerminal
3. Start custom application from the command line by prepending torsocks.
torsocks application-name
Using this method, there is no need to specify any proxy IP address, port number, protocol. [13]
Generic instructions for configuring custom installed applications for stream isolation for less than 7 custom applications using the application's proxy settings
- Install custom application.
- Configure application to use a dedicated Tor
SocksPortaccording to Torify HOWTO
by either configuring the application's proxy settings.
- protocol: socks 5
- Platform specific. Proxy IP: A) Non-Qubes-Whonix 10.152.152.10 B) Qubes-Whonix: Use the IP address returned by running the following command (NOTE: do not use the command itself): qubesdb-read /qubes-gateway
- port: 9153 (use a different port according to list above if using multiple custom installed applications)
- Start custom application.
Better generic instructions for this cannot be provided since this is application specific as mentioned above.
Better Protection
[edit]For best protection against identity correlation:
- Follow existing guidance: Read the advice above and on Whonix-Gateway.
- Disable desktop-wide proxy settings: Deactivate KDE / GNOME - application wide proxy settings because those proxy settings are not application specific, but rather force all KDE / GNOME applications through the same
SocksPort. There are no KDE / GNOME applications which use the internet preinstalled by default. However, deactivating those KDE / GNOME wide proxy settings gives finer control over stream isolation. - Disable transparent proxying: Disable transparent proxying as documented below.
Best Protection
[edit]Best stream isolation is only possible if you honor the advice above and only use one application per session and always revert to a fresh image or Multiple Whonix-Workstation. [12]
Disable Transparent Proxying
[edit]To deactivate transparent proxying, apply the following instructions.
Following these steps will disable the Whonix-Gateway transparent proxying feature and transform Whonix-Gateway into an IsolatingProxy![]()
.
Note: The following instructions should be applied in Whonix-Gateway (Qubes-Whonix™: In App Qubes sys-whonix).
1. Modify Whonix-Gateway User Firewall Settings.
Note: If no changes have yet been made to Whonix Firewall Settings, then the Whonix User Firewall Settings File /usr/local/etc/whonix_firewall.d/50_user.conf appears empty (because it does not exist). This is expected.
Select your platform.
Terminal Whonix-Gateway
In Whonix-Gateway, open the whonix_firewall configuration file in an editor.
sudoedit /usr/local/etc/whonix_firewall.d/50_user.conf
Qubes App Launcher (blue/grey "Q") → Whonix-Gateway App Qube (commonly called sys-whonix) → User Firewall Settings
For more help, press on Expand on the right.
Note: This is for informational purposes only! Do not edit /etc/whonix_firewall.d/30_whonix_gateway_default.conf.
Note: The Whonix Global Firewall Settings File /etc/whonix_firewall.d/30_whonix_gateway_default.conf contains default settings and explanatory comments about their purpose. By default, the file is opened read-only and is not meant to be directly edited. Below, it is recommended to open the file without root rights. The file contains an explanatory comment on how to change firewall settings.
## Please use "/etc/whonix_firewall.d/50_user.conf" for your custom configuration,
## which will override the defaults found here. When {{project_name_short}} is updated, this
## file may be overwritten.
See also Whonix modular flexible .d style configuration folders.
To view the file, follow these instructions.
If using Qubes-Whonix, complete these steps.
Qubes App Launcher (blue/grey "Q") → Template: whonix-gateway-18 → Global Firewall Settings
If using a graphical Whonix-Gateway, complete these steps.
Start Menu → Applications → Settings → Global Firewall Settings
If using a terminal Whonix-Gateway, complete these steps.
In Whonix-Gateway, view the global firewall configuration file in an editor. nano /etc/whonix_firewall.d/30_whonix_gateway_default.conf
2. Add.
WORKSTATION_TRANSPARENT_TCP=0 WORKSTATION_TRANSPARENT_DNS=0
3. Save.
4. Reload Whonix-Gateway Firewall.
Select your platform.
Qubes App Launcher (blue/grey "Q") → Whonix-Gateway ProxyVM (commonly named sys-whonix) → Reload Firewall
5. Done.
Deactivating transparent proxying is complete.
This will disable transparent proxying. All applications not configured to use a SocksPort by socks proxy settings or forced to use a SocksPort by a socksifier will not be able to establish connections. This is the only way to ensure that different SocksPorts are used and also that DNS is remotely resolved through that SocksPort.
6. Test.
Optional.
IsolateSOCKSAuth
[edit]See Tor manual![]()
IsolateSOCKSAuth.
Don’t share circuits with streams for which different SOCKS authentication was provided. [...]
This can be used with the SocksPort option.
SocksPort [address:]port|unix:path|auto [flags] [isolation flags]
IsolateSOCKSAuth is a sub option of the SocksPort option.
Qubes Specific
[edit]Qubes UpdatesProxy Stream Isolation
[edit]This chapter is for advanced users only.
Platform specific:
- Non-Qubes-Whonix:
apt-getis stream isolated by uwt and redirected to TorSocksPort. (See anon-ws-disable-stacked-tor.) Therefore, every VM uses a different stream, thanks to Tor's defaultIsolateClientAddroption, which results in different IP source addresses (different internal network VM IPs) getting stream isolated. - Qubes-Whonix: Security and stream isolation are unfortunately conflicting goals. Templates in Qubes are non-networked by default for better security because they do not have a network stack, hence a lower attack surface.
apt-getis redirected without a network through Qubes qrexec to Whonix-Gateway localhost, where Qubes tinyproxy is listening. Therefore, the information of the internal source IP address of the VM is "lost in translation" and does not reach Tor on Whonix-Gateway. Hence, there is no benefit fromIsolateClientAddr. tinyproxy on Whonix-Gateway has been configured to use a dedicated TorSocksPort
. That, of course, does not result in
IsolateClientAddr. But at least traffic by tinyproxy is not mixed into Tor'sTransPort/DnsPort. Unfortunately, all Templates usingsys-whonixas UpdatesProxy are mixed into the same stream. In conclusion, stream isolation ofapt-getin Qubes-Whonix is a bit worse than stream isolation in Non-Qubes-Whonix. This situation is unlikely to change due to the technical difficulty of improving it unless contributed. There are no known steps that users could take to improve this situation.- tinyproxy: Can use a Tor
SocksPort, which at least avoids mixing UpdatesProxy traffic into Tor'sTransPort/DnsPort. - apt-cacher-ng: Unsupported. Unknown if it can use
SocksPort. It might support an HTTP proxy, so a TorHTTPTunnelPortcould possibly be used. [15] - Remove tinyproxy idea: remove tinyproxy from Whonix-Gateway (
sys-whonix) and make Whonix Templates networked by default with Net qube set tosys-whonix
.
- User documentation: Qubes-Whonix UpdatesProxy user documentation
- Developer documentation: Torified UpdatesProxy developer documentation
- Future idea: Maybe in the future, after/if Create
sys-ops-whonixVM for Enhanced Security and Isolation in Qubes-Whonix
gets implemented,
sys-ops-whonixcould start a new instance of Qubes UpdatesProxy each time it receives a new connection from Qubes qrexec.
- tinyproxy: Can use a Tor
Deactivate Stream Isolation
[edit]Easy
[edit]Choose an option. Either A) or B).
- A) How to disable stream isolation. The easiest and most common methods only. Or,
- B) For more options, see below.
Deactivate uwt Stream Isolation Wrapper
[edit]OPTIONAL. Usually not required. Only for special setups and people who know what they are doing.
Temporary
[edit]anondist-orig Method
[edit]Append .anondist-orig to the command you want to run. For example, instead of using.
curl 38.229.72.22
Use.
curl.anondist-orig 38.229.72.22
Environment Variable Method
[edit]Use the UWT_DEV_PASSTHROUGH environment variable. [16]
Example. Set the UWT_DEV_PASSTHROUGH environment variable. This will disable using torsocks for all subsequent invocations.
export UWT_DEV_PASSTHROUGH="1" curl 38.229.72.22
When running as user and using sudo, do not forget the sudo parameter -E which stands for preserve environment.
sudo -E apt update
Permanently
[edit]Introduction
[edit]You can enable/disable all uwt stream isolation wrappers globally or enable/disable specific stream isolation wrappers, see uwt /etc/uwt.d/30_uwt_default.conf configuration file.
deactivate all uwt wrappers permanently
[edit]The following instructions permanently deactivate all uwt wrappers and remove stream isolation for uwt-wrapped applications system-wide. Consequently, all uwt-wrapped applications revert to the default system networking configuration.
For more granular control of uwt wrapper deactivation, see: Deactivate uwt Stream Isolation Wrapper.
1. Platform specific notice:
- Non-Qubes-Whonix™: No platform specific notice.
- Qubes-Whonix™: In Template. (
whonix-workstation-18) [17]
2. Open file /etc/uwt.d/50_user.conf in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/uwt.d/50_user.conf
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/uwt.d/50_user.conf
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/uwt.d/50_user.conf
3. Add.
uwtwrapper_global="0"
4. Save and exit.
5. Check that the changes have taken effect. Run in terminal: uwt_settings_show
It should print
uwt INFO: disabled.
6. Done.
Deactivate Misc Proxy Settings
[edit]On the Stream Isolation page, there is a list of applications that are pre-configured to use socks proxy settings via application configuration files. To disable this the Whonix system default must be removed from the application's settings.
TODO: document and expand.
Remove proxy settings for APT repository files.
1. Platform specific notice:
- Non-Qubes-Whonix™: No platform specific notice.
- Qubes-Whonix™: In Template. (
whonix-workstation-18)
2. If you previously onionized any repositories, that has to be undone; see Onionizing Repositories.
3. Remove any mention of tor+ in file /etc/apt/sources.list (if it was previously configured; that file is empty by default in Whonix / Kicksecure) or any file in folder /etc/apt/sources.list.d.
4. Open file /etc/apt/sources.list /etc/apt/sources.list.d/* in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/apt/sources.list /etc/apt/sources.list.d/*
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/apt/sources.list /etc/apt/sources.list.d/*
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/apt/sources.list /etc/apt/sources.list.d/*
5. Remove any mention of tor+.
6. Done.
The process of removing proxy settings from APT repository files is now complete.
Remove proxy settings for Tor Browser Downloader by Whonix.
1. Platform specific notice:
- Non-Qubes-Whonix: No platform specific notice.
- Qubes-Whonix: In Template. (
whonix-workstation-18) [18]
2. Open file /etc/torbrowser.d/50_user.conf in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/torbrowser.d/50_user.conf
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/torbrowser.d/50_user.conf
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/torbrowser.d/50_user.conf
TB_NO_TOR_CON_CHECK=1 CURL_PROXY="--fail"
4. Save and exit.
5. Done.
Proxy settings have been removed from Tor Browser Downloader by Whonix (and Mullvad Browser by Kicksecure developers).
For some applications, this is impossible:
These applications can only talk to Tor Onion Services directly and cannot be configured to use the system default. Therefore you can only deactivate sdwdate and/or not use applications like OnionShare and Ricochet IM.
Tor Browser Remove Proxy Settings
[edit]If you would like to remove proxy settings from Tor Browser, see below.
Introduction
This configuration results in Tor Browser no longer using proxy settings. With no proxy set, Tor Browser uses the (VM) system's default networking. This is identical to any other application inside Whonix-Workstation™ that has not been explicitly configured to use Tor via socks proxy settings or a socksifier. This setting is also called transparent torification. [21] [22]
Note: This action will break both Stream Isolation for Tor Browser and Tor Browser's SOCKS username for a request based on first party domain![]()
feature. This worsens the web fingerprint and leads to pseudonymous (not anonymous) connections. To mitigate these risks, consider using More than one Tor Browser in Whonix, or preferably Multiple Whonix-Workstation™.
Local socks proxy Method
This method works for removal of proxy settings but is rather lengthy and complicated. In case the user wants to have a look anyhow, please press on Expand on the right.
Since other methods to configure Tor Browser to use system default networking are broken due to Tor Browser changes by upstream, this new local socks proxy method stops anon-ws-disable-stacked-tor local port 9150 redirection to Whonix-Gateway™ 9150 (where a Tor SocksPort is listening). As a replacement, a local socks proxy listens on Whonix-Workstation local port 9150 which then forwards the traffic using system default networking. In result, if the user is using a VPN inside Whonix-Workstation or in a VPN-Gateway wretched between Whonix-Gateway™ and Whonix-Workstation, Tor Browser would use the VPN.
In this documentation, Dante is used as a local socks proxy. Development notes are kept on Dev/Dante.
1. Legacy notices.
- New users, that did not apply instructions from this page again: No special notice.
- Existing users: See below.
A few settings need to be undone.
- A) Previous changes to
/etc/environmentas documented previously for other methods need to be undone. - B) Tor Browser needs to be re-installed. This is because undoing the previous configuration is difficult and undocumented.
2. Stop default anon-ws-disable-stacked-tor service for port 9150.
- Non-Qubes-Whonix: In Whonix-Workstation.
- Qubes-Whonix: In
whonix-workstation-18Template.
sudo systemctl stop anon-ws-disable-stacked-tor_autogen_port_9150.socket sudo systemctl stop anon-ws-disable-stacked-tor_autogen_port_9150.service sudo systemctl stop anon-ws-disable-stacked-tor_autogen__run_anon-ws-disable-stacked-tor_127.0.0.1_9150.sock.socket sudo systemctl stop anon-ws-disable-stacked-tor_autogen__run_anon-ws-disable-stacked-tor_127.0.0.1_9150.sock.service
3. Prevent default anon-ws-disable-stacked-tor systemd unit from starting.
- Non-Qubes-Whonix: In Whonix-Workstation.
- Qubes-Whonix: In
whonix-workstation-18Template.
sudo systemctl mask anon-ws-disable-stacked-tor_autogen_port_9150.socket sudo systemctl mask anon-ws-disable-stacked-tor_autogen_port_9150.service sudo systemctl mask anon-ws-disable-stacked-tor_autogen__run_anon-ws-disable-stacked-tor_127.0.0.1_9150.sock.socket sudo systemctl mask anon-ws-disable-stacked-tor_autogen__run_anon-ws-disable-stacked-tor_127.0.0.1_9150.sock.service
4. Install the local socks proxy server.
- Non-Qubes-Whonix: In Whonix-Workstation.
- Qubes-Whonix: In
whonix-workstation-18Template.
A) Enable Debian source repository.
Open file /etc/apt/sources.list.d/debian.sources in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/apt/sources.list.d/debian.sources
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/apt/sources.list.d/debian.sources
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/apt/sources.list.d/debian.sources
Find and edit the following stanza (around lines 69-74).
Types: deb-src URIs: tor+https://deb.debian.org/debian Suites: trixie trixie-updates trixie-backports Components: main contrib non-free non-free-firmware Enabled: yes # <<<<< change this line from "no" to "yes" Signed-By: /usr/share/keyrings/debian-archive-keyrings.gpg
Save and exit.
sudo apt update
B) Install build dependencies.
sudo apt build-dep dante-server
C) Get dante source code.
apt-get source dante-server
D) Open the dante accesscheck.c source file.
mousepad ~/dante-1.4.2+dfsg/sockd/accesscheck.c
Paste the contents. Here we rewrite the authentication method to always return true. For the reasons see Dev/Dante.
/* * Copyright (c) 1997, 1998, 1999, 2000, 2001, 2002, 2003, 2005, 2006, 2008, * 2009, 2010, 2011, 2012, 2013 * Inferno Nettverk A/S, Norway. All rights reserved. * * Redistribution and use in source and binary forms, with or without * modification, are permitted provided that the following conditions * are met: * 1. The above copyright notice, this list of conditions and the following * disclaimer must appear in all copies of the software, derivative works * or modified versions, and any portions thereof, aswell as in all * supporting documentation. * 2. All advertising materials mentioning features or use of this software * must display the following acknowledgement: * This product includes software developed by * Inferno Nettverk A/S, Norway. * 3. The name of the author may not be used to endorse or promote products * derived from this software without specific prior written permission. * * THIS SOFTWARE IS PROVIDED BY THE AUTHOR ``AS IS'' AND ANY EXPRESS OR * IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES * OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. * IN NO EVENT SHALL THE AUTHOR BE LIABLE FOR ANY DIRECT, INDIRECT, * INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT * NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, * DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY * THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT * (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF * THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. * * Inferno Nettverk A/S requests users of this software to return to * * Software Distribution Coordinator or sdc@inet.no * Inferno Nettverk A/S * Oslo Research Park * Gaustadalléen 21 * NO-0349 Oslo * Norway * * any improvements or extensions that they make and grant Inferno Nettverk A/S * the rights to redistribute these changes. * */ #include "common.h" static const char rcsid[] = "$Id: accesscheck.c,v 1.89 2013/10/27 15:24:42 karls Exp $"; int usermatch(auth, userlist) const authmethod_t *auth; const linkedname_t *userlist; { /* const char *function = "usermatch()"; */ const char *name; if ((name = authname(auth)) == NULL) return 0; /* no username, no match. */ do if (strcmp(name, userlist->name) == 0) break; while ((userlist = userlist->next) != NULL); if (userlist == NULL) return 0; /* no match. */ return 1; } int groupmatch(auth, grouplist) const authmethod_t *auth; const linkedname_t *grouplist; { const char *function = "groupmatch()"; const char *username; struct passwd *pw; struct group *groupent; SASSERTX(grouplist != NULL); if ((username = authname(auth)) == NULL) return 0; /* no username, no match. */ /* * First check the primary group of the user against grouplist. * If the groupname given there matches, we don't need to go through * all users in the list of group. */ if ((pw = getpwnam(username)) != NULL && (groupent = getgrgid(pw->pw_gid)) != NULL) { const linkedname_t *listent = grouplist; do if (strcmp(groupent->gr_name, listent->name) == 0) return 1; while ((listent = listent->next) != NULL); } else { if (pw == NULL) slog(LOG_DEBUG, "%s: unknown username \"%s\"", function, username); else if (groupent == NULL) slog(LOG_DEBUG, "%s: unknown primary groupid %ld", function, (long)pw->pw_gid); } /* * Go through grouplist, matching username against each groupmember of * all the groups in grouplist. */ do { char **groupname; if ((groupent = getgrnam(grouplist->name)) == NULL) { swarn("%s: unknown groupname \"%s\"", function, grouplist->name); continue; } groupname = groupent->gr_mem; while (*groupname != NULL) { if (strcmp(username, *groupname) == 0) return 1; /* match. */ ++groupname; } } while ((grouplist = grouplist->next) != NULL); return 0; } #if HAVE_LDAP int ldapgroupmatch(auth, rule) const authmethod_t *auth; const rule_t *rule; { const char *function = "ldapgroupmatch()"; const linkedname_t *grouplist; const char *username; char *userdomain, *groupdomain; int retval; if ((username = authname(auth)) == NULL) return 0; /* no username, no match. */ #if !HAVE_GSSAPI if (!rule->state.ldap.ldapurl) SERRX(rule->state.ldap.ldapurl != NULL); #endif /* !HAVE_GSSAPI */ if ((userdomain = strchr(username, '@')) != NULL) ++userdomain; if (userdomain == NULL && *rule->state.ldap.domain == NUL && rule->state.ldap.ldapurl == NULL) { slog(LOG_DEBUG, "%s: cannot check ldap group membership for user %s: " "user has no domain postfix and no ldap url is defined", function, username); return 0; } if ((retval = ldap_user_is_cached(username)) >= 0) return retval; /* go through grouplist, matching username against members of each group. */ grouplist = rule->ldapgroup; do { char groupname[MAXNAMELEN]; slog(LOG_DEBUG, "%s: checking if user %s is member of ldap group %s", function, username, grouplist->name); STRCPY_ASSERTLEN(groupname, grouplist->name); if ((groupdomain = strchr(groupname, '@')) != NULL) { *groupdomain = NUL; /* separates groupname from groupdomain. */ ++groupdomain; } if (groupdomain != NULL && userdomain != NULL) { if (strcmp(groupdomain, userdomain) != 0 && strcmp(groupdomain, "") != 0) { slog(LOG_DEBUG, "%s: userdomain \"%s\" does not match groupdomain " "\"%s\" and groupdomain is not default domain. " "Trying next entry", function, userdomain, groupdomain); continue; } } if (ldapgroupmatches(username, userdomain, groupname, groupdomain, rule)){ cache_ldap_user(username, 1); return 1; } } while ((grouplist = grouplist->next) != NULL); cache_ldap_user(username, 0); return 0; } #endif /* HAVE_LDAP */ int accesscheck(s, auth, src, dst, emsg, emsgsize) int s; authmethod_t *auth; const struct sockaddr_storage *src, *dst; char *emsg; size_t emsgsize; { int match, authresultisfixed; match = 1; /* * HACK-FORK-EDIT-OK */ return match; }
E) Change directory into the dante source code folder.
pushd dante-1.4.2+dfsg
F) Build the Debian package.
dpkg-buildpackage -b --no-sign
E) Change directory back to the home folder.
popd
F) Install the modified dante package.
sudo dpkg -i dante-server_1.4.2+dfsg-7_amd64.deb
G) Block updates of dante-server.
sudo apt-mark hold dante-server
5. Open file /etc/danted.conf in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/danted.conf
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/danted.conf
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/danted.conf
6. Local socks proxy configuration.
- Non-Qubes-Whonix: In Whonix-Workstation.
- Qubes-Whonix: In
whonix-workstation-18Template.
Delete all contents from the file and replace it with the following configuration.
debug: 0 logoutput: stderr internal: 127.0.0.1 port = 9150 external: eth0 socksmethod: none username clientmethod: none user.privileged: root user.notprivileged: root user.libwrap: root # allow connections only from localhost client pass { from: 127.0.0.1/8 port 1-65535 to: 0.0.0.0/0 log: connect disconnect error # comment on some logs if you don't want to keep them } socks pass { from: 0.0.0.0/0 to: 0.0.0.0/0 command: bind connect udpassociate log: error connect disconnect iooperation }
7. Restart the local socks proxy.
This is to apply the changed configuration and to test if the configuration is valid.
- Non-Qubes-Whonix: In Whonix-Workstation.
- Qubes-Whonix: In
whonix-workstation-18Template.
sudo systemctl restart danted.service
8. tb-starter Configuration
- Non-Qubes-Whonix: In Whonix-Workstation.
- Qubes-Whonix: In
whonix-workstation-18Template.
Stop Tor from using unix domain socket files for socks so it uses socks on IP 127.0.0.1 port 9150 instead.
Open file /etc/torbrowser.d/50_user.conf in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/torbrowser.d/50_user.conf
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/torbrowser.d/50_user.conf
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/torbrowser.d/50_user.conf
Paste.
unset TOR_SOCKS_IPC_PATH
Save and exit.
9. Platform specific notice:
- Non-Qubes-Whonix: No special notice required.
- Qubes-Whonix: Shutdown Template. Once done, restart App Qube.
10. Start Tor Browser.
- Non-Qubes-Whonix: In Whonix-Workstation.
- Qubes-Whonix: In
Whonix-WorkstationApp Qube.
torbrowser
Tor Browser should now be using system default networking thanks to the local socks proxy.
No additional configuration of Tor Browser is required.
11. Done.
Older Methods:
For older methods, which might be broken due to Tor Browser changes by upstream, please press on Expand on the right.
To enable transparent torification (no proxy setting), set the TOR_TRANSPROXY=1 environment variable. There are several methods, but the simplest is the /etc/environment Method.
Note: Choose only one method to enable transparent torification.
/etc/environment Method
This will apply to the whole environment, including any possible custom locations of Tor Browser installation folders. [23]
1. Platform specific notice.
- Non-Qubes-Whonix™: No platform specific notice.
- Qubes-Whonix™: In Template. (
whonix-workstation-18)
2. Open file /etc/environment in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/environment
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/environment
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/environment
3. Add the following line.
TOR_TRANSPROXY=1 ## newline at the end
4. Save and exit.
5. Reboot.
Reboot is required to make changes to configuration file /etc/environment take effect.
6. Done.
/etc/environment method configuration has been completed.
Tor Browser Settings Changes
This step is required since Tor Browser 10. [24]
1. Platform specific notice.
- Non-Qubes-Whonix: No platform specific notice.
- Qubes-Whonix: In App Qube. (
anon-whonix)
2. Tor Browser → URL bar → Type: about:config → Press Enter key. → search for and modify
3. network.dns.disabled → set to false
4. extensions.torbutton.launch_warning → set to false
Undo
Reverting this change is undocumented. Simply unsetting that environment variable will not work due to Tor Browser limitations. The easiest way to undo this setting is to install a fresh instance of Tor Browser (please contribute to these instructions)!
Command Line Method
1. Platform specific notice:
- Non-Qubes-Whonix: No platform specific notice.
- Qubes-Whonix: In App Qube. (
anon-whonix)
2. Navigate to the Tor Browser folder.
cd ~/.tb/tor-browser
3. Every time Tor Browser is started, run the following command to set the TOR_TRANSPROXY=1 environment variable.
TOR_TRANSPROXY=1 ./start-tor-browser.desktop
4. Done.
start-tor-browser Method
This only applies to a single instance of the Tor Browser folder that is configured. This method may not persist when Tor Browser is updated.
1. Platform specific notice:
- Non-Qubes-Whonix: No platform specific notice.
- Qubes-Whonix: In App Qube. (
anon-whonix)
2. Find and open start-tor-browser in the Tor Browser folder with an editor.
This is most likely found in ~/.tb/tor-browser/Browser/start-tor-browser below #!/usr/bin/env bash.
3. Set.
export TOR_TRANSPROXY=1
4. Done.
start-tor-browser Method configuration has been completed.
Ignore Tor Button's Open Network Settings
Whonix has disabled the Open Network Settings... menu option in Tor Button. Read the footnote for further information. [25]
Nested Execution
[edit]uwt version 4.0-1 and above protects from endless nested execution which could likely lead to a locked up session by aborting after 10 times an uwt wrapped application calling another uwt wrapped application. In that case, you would see the following error message.
uwtwrapper uwt wrapper ERROR: More than uwtwrapper_counter 10 nested executions (uwtwrapper_max: 10).
This is most likely happening due to two symlinks pointing to each other, resulting in endless execution. However, should there be any cases (none could be foreseen at development time) where this is legitimate, feel free to change the setting responsible for aborting execution. Please also consider reporting your use case in Whonix forums so perhaps a better fix for this can be found.
Open file /etc/uwt.d/50_user.conf in an editor with administrative ("root") rights.
1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /etc/uwt.d/50_user.conf
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /etc/uwt.d/50_user.conf
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /etc/uwt.d/50_user.conf
Set uwtwrapper_max to a value more suitable for you.
uwtwrapper_max=100
Alternatively you could completely disable the nested execution protection.
nested_protection() { true }
Save and exit.
Done.
Development
[edit]Information
[edit]See also the Tor manual![]()
on
SocksPort, HTTPTunnelPort, TransPort and DnsPort.
SocksPort
[edit]A SocksPort is a listen port by Tor which accepts traffic using the socks![]()
protocol.
Using a SocksPort is possible by using either:
- application specific socks proxy settings

- wrapper method

such as
torsocks(which can be automatically prepended usinguwt
)
Traffic on separate SocksPorts is stream isolated by Tor by default.
HTTPTunnelPort
[edit]A HTTPTunnelPort is a listen port by Tor which accepts traffic using the HTTP CONNECT method![]()
.
This is a new feature of Tor.
Traffic on separate HTTPTunnelPorts is stream isolated by Tor by default.
Forum discussion:
https://forums.whonix.org/t/tor-can-now-serve-as-http-proxy-httptunnelport/5373![]()
TransPort
[edit]TransPort is a feature where Tor accepts raw traffic on a listen port if redirected there using iptables. See also TransparentProxy![]()
.
When using Transparent Proxying (default in Whonix), all applications that do not use a SocksPort or HTTPTunnelPort will fall back to using Tor's TransPort for TCP. I.e. using system default networking. This is also called transparent proxying.
There is no stream isolation for TransPort connections unless originating from a separate Whonix-Workstation. [12]
DnsPort
[edit]Similar to above but for DNS. All applications that do not use a SocksPort or HTTPTunnelPort will fall back to using Tor's DnsPort for DNS.
torsocks
[edit]All uwt wrapped applications will be stream isolated by torsocks![]()
/etc/tor/torsocks.conf setting IsolatePID 1.
To test this, run the following command multiple times.
scurl https://check.torproject.org | grep IP
Tests
[edit]1. Applications which internally use curl.
sudo update-command-not-found sudo update-flashplugin-nonfree --install --verbose
2. Applications which are uwt wrapped themselves and internally use ssh.
git push origin master
3. Enigmail.
Debugging / List of all uwt wrappers
[edit]sudo dpkg-divert --list ls -la /usr/bin/ssh
Deactivating an uwt wrapper
[edit]Example:
sudo unlink /usr/bin/ssh sudo dpkg-divert --rename --remove /usr/bin/ssh
Check if Transparent DNS is disabled
[edit]Note: The following test should be performed in Whonix-Workstation (Qubes-Whonix: App Qube anon-whonix).
Test.
nslookup check.torproject.org ; echo $?
Expected output.
;; connection timed out; no servers could be reached 1
If it shows something else, such as a resolved IP, then Transparent DNS is enabled.
Check if Transparent TCP is disabled
[edit]Note: The following test should be performed in Whonix-Workstation (Qubes-Whonix: App Qube anon-whonix).
Test.
UWT_DEV_PASSTHROUGH=1 curl 116.202.120.181 ; echo $?
Expected output.
curl: (7) couldn't connect to host 7
If it shows something else, such as the html source code, then Transparent TCP is enabled.
Check if Transparent Proxying is disabled
[edit]Note: The following test should be performed in Whonix-Workstation (Qubes-Whonix: App Qube anon-whonix).
Test.
UWT_DEV_PASSTHROUGH=1 curl https://check.torproject.org/ ; echo $?
Expected output.
curl: (6) Couldn't resolve host 'check.torproject.org' 6
If it shows something else, such as the html source code, then Transparent Proxying is enabled.
Check if an Application is properly using Stream Isolation
[edit]- Same as
leak testingas if Whonix is not involved. - Also... A weaker test... The
transparent proxying disablementtest.
Disable transparent proxying of DNS and TCP as per #Better Protection.
Check that worked as per:
That is because it doesn't work without transparent proxying (system default networking), meaning if the application is unable to use the network normally, then there is a certain socks leak, meaning certainly some traffic which requires system default networking. In case of:
- clearnet operating systems: a clearnet leak
- Whonix: a stream isolation violation
This is only a weak test since an application could very likely try socks first and, if socks fails, fall back to system default networking. Therefore, normal leak testing is required.
- Internet research if application was specifically designed for use with Tor.
- Internet research if application was specifically audited for clearnet leaks.
- Discussion with software contributor about this if these haven't already happened.
- https://gitlab.torproject.org/legacy/trac/-/wikis/doc/TorifyHOWTO#Howtoreviewanapplication

- https://lists.torproject.org/pipermail/tor-talk/2012-April/024010.html

- https://gitlab.torproject.org/legacy/trac/-/issues/5553

- corridor - Tor traffic whitelisting gateway

Add new uwt wrapper
[edit]Emulate this commit![]()
.
Sources
[edit]- Separate streams across circuits by connection metadata

- tor-talk Operating system updates / software installation behind Tor Transparent Proxy

- tor-talk Awareness for identity correlation through circuit sharing is almost zero.

- tor-talk Tor's stream isolation features defaults Question

- tor-talk Tor's stream isolation features defaults Answer

- Tails-dev separate Tor streams

- Tails separate Tor streams

- Tails-dev Please review Tails stream isolation plans

- Tails Design: Tor stream isolation

Stream Isolation Graphic was contributed by: Cuan Knaggs, graphic and web design. revolver![]() print media, web design, web development, CMS, e-commerce
print media, web design, web development, CMS, e-commerce
References
[edit]- ↑ Tails used to have transparent proxying (could use any application without configuration). Nowadays Tails has no transparent proxying. (Most) Custom installed applications (example: Mozilla Firefox) won't connect without manual configuration in Tails.
- ↑ Whonix-Workstation 127.0.0.1:9150 gets redirected to 10.152.152.10:9150 by anon-ws-disable-stacked-tor

. Changing proxy settings in Tor Browser has proven to be unreliable. At some point Tor Button may change its internals and therefore break something again. Keeping the default settings and not requiring any changes in Tor Browser seems like the best way to support compatibility in the long run and also is simplest in case update-torbrowser breaks and manually updating Tor Browser is required again in future.
- ↑
- ↑ 4.0 4.1
systemcheck --leak-testsruns only on user request and never by its own by chance. Tests two things, a TorSocksPortand Tor'sTransPort.SocksPorttest usesSOCKS_PORT_SYSTEMCHECK9110. Stream isolating transparent proxying, the TorTransPortleak test is impossible. The whole point of the leak test is to check if connections not configured to use a TorSocksPortwill be torified or not. - ↑
This feature does not even require Tor
ControlPortaccess. All that Tor Browser requires from Whonix is being able to connect to a TorSocksPort. - ↑
https://gitlab.torproject.org/legacy/trac/-/issues/3455

- ↑
https://lists.torproject.org/pipermail/tor-talk/2012-September/025432.html

- ↑
This assumes the application properly supports Tor and uses stream isolation mechanisms such as
IsolateSOCKSAuth. - ↑
If you used to use only one
SocksPortwith the common torification methods
, the same thing happened

.
- ↑
Tor configuration file
/etc/torrc.d/70_workstation.conf%includes file/usr/share/tor/tor-service-defaults-torrc.anondist. - ↑ What about UDP? See Tor#UDP.
- ↑ 12.0 12.1 12.2
Multiple Whonix-Workstation using different internal IP's are automatically separated by Tor (
IsolateClientAddris Tor's default). - ↑
This is because
torsocksconfiguration file/etc/tor/torsocks.conf.anondist
is preconfigured with setting
IsolatePID 1.# Set Torsocks to use an automatically generated SOCKS5 username/password based # on the process ID and current time, that makes the connections to Tor use a # different circuit from other existing streams in Tor on a per-process basis. # If set, the SOCKS5Username and SOCKS5Password options must not be set. # (Default: 0) IsolatePID 1
- ↑
Although not strictly required, you could alternatively/additionally deactivate Tor
TransPortandDnsPort. Add to /usr/local/etc/torrc.d/50_user.conf. Tor configuration file.Open the file
/usr/local/etc/torrc.d/50_user.confin a text editor of your choice with administrative rights.
of your choice with administrative rights.
1 Sysmaint notice.
Ensure the VM has administrative (
sudo/root) access first. See also sysmaint.2 Platform specific. Select your platform.
Graphical Whonix-Gateway SYSMAINT Session
If you are using a graphical Whonix-Gateway booted into
PERSISTENT Mode | SYSMAINT Session, take the following step.System Maintenance Panel→Open Terminal→ run/usr/libexec/gateway-shortcuts/torrcGraphical Whonix-Gateway Unrestricted Admin Mode
If you are using a graphical Whonix-Gateway and enabled unrestricted admin mode
 , take the following step.
, take the following step.
Start Menu→System Tools→Tor User ConfigIf you are using Qubes-Whonix™, take the following step.
Qubes App Launcher (blue/grey "Q")→Service→Whonix-Gateway™ ProxyVM (commonly named sys-whonix)→Tor User ConfigAdd.
TransPort 0 DnsPort 0
Save.
And then Reload Tor.
After changing Tor configuration, Tor must be reloaded for changes to take effect.
Note: If Tor does not connect after completing all these steps, then a user mistake is the most likely explanation. Recheck
/usr/local/etc/torrc.d/50_user.confand repeat the steps outlined in the sections above. If Tor then connects successfully, all the necessary changes have been made.If you are using Qubes-Whonix™, complete the following steps.
Qubes App Launcher (blue/grey "Q")→Service→Whonix-Gateway™ ProxyVM (commonly named 'sys-whonix')→Reload TorIf you are using a graphical Whonix-Gateway, complete the following steps.
Start Menu→System Tools→Reload TorIf you are using a terminal Whonix-Gateway, click
HEREfor instructions.Complete the following steps.
Reload Tor.
sudo systemctl reload tor@default.service
Check Tor's daemon status.
sudo systemctl status tor@default.service
It should include a a message saying.
Active: active (running) since ...
In case of issues, try the following debugging steps.
Check Tor's config.
sudo -u debian-tor tor --verify-config
The output should be similar to the following.
Sep 17 17:40:41.416 [notice] Read configuration file "/usr/local/etc/torrc.d/50_user.conf". Configuration was valid
- ↑
https://forums.whonix.org/t/tor-can-now-serve-as-http-proxy-httptunnelport/5373

- ↑ https://github.com/Whonix/uwt/blob/master/usr/libexec/uwt/uwtwrapper#L194

- ↑
Qubes-Whonix users note: Or alternatively in App Qube.
1. Create folder
/usr/local/etc/uwt.d.sudo mkdir -p /usr/local/etc/uwt.d
2. Open with root rights: sudoedit /usr/local/etc/uwt.d/50_user.conf
- ↑
Qubes-Whonix users note: In App Qube (
whonix-workstation-18) could also use file/usr/local/etc/torbrowser.d/50_user.confinstead.1. Create folder
/usr/local/etc/torbrowser.d(if using Tor Browser Downloader by Whonix developers) and optionally/usr/local/etc/mullvadbrowser.d(if using Mullvad Browser by Kicksecure developers).mkdir -p /usr/local/etc/torbrowser.d
mkdir -p /usr/local/etc/mullvadbrowser.d
2. Open file
/usr/local/etc/torbrowser.d/50_user.confin an editor with administrative ("root") rights.1 Select your platform.
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand.
3 Open the file with root rights.
sudoedit /usr/local/etc/torbrowser.d/50_user.conf
2 Notes.
- Sudoedit guidance: See Open File with Root Rights
 for details on why using
for details on why using sudoeditimproves security and how to use it. - Editor requirement: Close Featherpad (or the chosen text editor) before running the
sudoeditcommand. - Template requirement: When using Qubes-Whonix, this must be done inside the Template.
3 Open the file with root rights.
sudoedit /usr/local/etc/torbrowser.d/50_user.conf
4 Notes.
- Shut down Template: After applying this change, shut down the Template.
- Restart App Qubes: All App Qubes based on the Template need to be restarted if they were already running.
- Qubes persistence: See also Qubes Persistence

- General procedure: This is a general procedure required for Qubes and is unspecific to Qubes-Whonix.
2 Notes.
- Example only: This is just an example. Other tools could achieve the same goal.
- Troubleshooting and alternatives: If this example does not work for you, or if you are not using Whonix, please refer to Open File with Root Rights.
3 Open the file with root rights.
sudoedit /usr/local/etc/torbrowser.d/50_user.conf
And/or:
sudoedit /usr/local/etc/mullvadbrowser.d/50_user.conf
- Sudoedit guidance: See Open File with Root Rights
- ↑
TB_NO_TOR_CON_CHECK=1needs to be set because there is no filtered Tor ControlPort access when Whonix tunnel firewall is enabled, which would break tb-updater's Tor connectivity check. - ↑
By tb-updater default, if unset, variable
CURL_PROXYwill be dynamically set to a Tor SocksPort on Whonix-Gateway™. For example toCURL_PROXY="--proxy socks5h://user:password@10.137.6.1:9115".
By utilizing a curl parameter we are using anyhow --CURL_PROXY="--fail"-- the environment variable can be disabled even if it is technically still set. This will result in downloading via the system's default networking. - ↑
This term was coined in context of a Tor Transparent Proxy

(.onion
 ). It acts as a simple gateway that routes all connections through Tor, but does not provide Stream Isolation.
). It acts as a simple gateway that routes all connections through Tor, but does not provide Stream Isolation.
- ↑ If these settings are changed, Tor Button would previously show a red sign and state "Tor Disabled" when a mouse was hovered over it.
- ↑ Unless this environment variable is manually unset before starting Tor Browser.
- ↑
- ↑ The regular Tor Browser Bundle from The Tor Project (without Whonix) allows networking settings to changed inside Tor via the
Open Network Settingsmenu option. It has the same effect as editing Tor's config file torrc. In Whonix, the environment variableexport TOR_NO_DISPLAY_NETWORK_SETTINGS=1has been set
to disable the
Tor Browser→Open Network Settings...menu item. It is not useful and confusing to have in the Whonix-Workstation because:- In Whonix, there is only limited access to Tor's control port (see onion-grater, a Tor Control Port Filter Proxy, design documentation for more information).
- For security reasons, Tor must be manually configured in /usr/local/etc/torrc.d/50_user.conf on Whonix-Gateway, and not from Whonix-Workstation (see VPN/Tunnel support for more information).

We believe security software like Whonix needs to remain Open Source and independent. Would you help sustain and grow the project? Learn more about our 14 year success story and maybe DONATE!